Network security firms have become essential partners for small businesses navigating an increasingly complex threat landscape. As cyberattacks grow more sophisticated and frequent, organizations across industries rely on specialized security providers to protect their digital assets, customer data, and operational continuity. For businesses in Lethbridge and surrounding areas, understanding what these firms offer and how to evaluate their capabilities can make the difference between maintaining secure operations and experiencing costly breaches that damage reputation and revenue.
Understanding What Network Security Firms Provide
Network security firms specialize in protecting organizational IT infrastructure from unauthorized access, data breaches, malware, and other cyber threats. These companies deploy a combination of technology solutions, expert personnel, and proactive monitoring to create defense-in-depth strategies tailored to each client's needs.
The scope of services varies significantly across providers. Some firms focus exclusively on perimeter defense through firewalls and intrusion detection systems, while others offer comprehensive managed security services that encompass everything from endpoint protection to incident response. The most effective providers take a holistic approach that addresses network architecture, user behavior, policy development, and continuous monitoring.
Core Service Offerings
Modern network security firms typically provide several foundational services that small businesses should prioritize:
- Firewall management and configuration following industry best practices
- Intrusion detection and prevention systems (IDS/IPS) that identify suspicious activity
- Virtual private network (VPN) deployment for secure remote access
- Security information and event management (SIEM) for centralized logging
- Vulnerability assessment and penetration testing to identify weaknesses
- Endpoint protection across workstations, servers, and mobile devices
These services work together to create multiple security layers. When one control fails, others remain in place to prevent or detect breaches before significant damage occurs.

Evaluating Network Security Firms for Your Business
Selecting the right security partner requires careful consideration of multiple factors beyond price. Small businesses must assess technical capabilities, industry experience, response times, and cultural fit to ensure long-term success.
Start with certifications and credentials. Reputable network security firms employ professionals with recognized certifications such as CISSP (Certified Information Systems Security Professional), CEH (Certified Ethical Hacker), and CISM (Certified Information Security Manager). These credentials demonstrate commitment to professional standards and ongoing education.
Key Selection Criteria
| Criteria | What to Look For | Why It Matters |
|---|---|---|
| Experience | 5+ years in your industry | Industry-specific threats require specialized knowledge |
| Response Time | 24/7 monitoring with <1 hour response | Breaches escalate quickly; immediate response limits damage |
| Compliance Knowledge | Familiarity with relevant regulations | Avoid fines and maintain customer trust |
| Scalability | Solutions that grow with your business | Prevents costly migrations as needs evolve |
| Transparency | Clear reporting and communication | Enables informed decision-making |
Geographic proximity matters for small businesses seeking personalized service. While many security functions can be delivered remotely, having a provider familiar with local business conditions and available for on-site emergencies provides significant advantages.
Questions to Ask Potential Providers
Before committing to a contract, interview multiple network security firms and ask specific questions about their approach:
- How do you stay current with emerging threats and attack vectors?
- What is your average response time for security incidents?
- Can you provide references from businesses similar to ours?
- How do you handle after-hours emergencies?
- What metrics do you use to measure security effectiveness?
- How often do you conduct security assessments and audits?
The quality of responses reveals much about a firm's operational maturity and client focus. Vague answers or reluctance to provide specific examples should raise concerns.
Essential Security Practices Firms Implement
The network security market continues to expand as organizations recognize the critical importance of robust defenses. Leading network security firms implement proven practices that form the foundation of effective protection strategies.
Network segmentation stands as one of the most powerful security controls available. By dividing networks into isolated segments, firms limit lateral movement by attackers who gain initial access. This approach, detailed in Harvard’s network security best practices guide, ensures that compromising one system doesn't automatically expose all resources.
Firewall Configuration Standards
Proper firewall configuration requires adherence to strict principles that many businesses overlook. The six network firewall configuration best practices emphasize blocking traffic by default and only allowing specifically authorized communications.
- Implement default-deny policies for all inbound and outbound traffic
- Apply the principle of least privilege to every access rule
- Maintain detailed documentation of all firewall rules and their business justifications
- Schedule regular rule reviews to eliminate outdated or unnecessary permissions
- Enable comprehensive logging for security analysis and compliance
- Test configuration changes in isolated environments before production deployment
Network security firms bring specialized expertise to these technical requirements, ensuring configurations align with both security needs and business operations. Small businesses often lack the in-house expertise to maintain these standards consistently.

Authentication and Access Controls
Multi-factor authentication (MFA) has transitioned from optional enhancement to mandatory control. Network security firms enforce MFA across all access points, particularly for administrative accounts and remote connections. This single control prevents the vast majority of credential-based attacks.
Access management extends beyond authentication to include:
- Role-based access control (RBAC) that grants permissions based on job functions
- Privileged access management (PAM) for administrative accounts
- Regular access reviews to remove unused accounts and excessive permissions
- Strong password policies enforced through technical controls
- Account lockout mechanisms after failed login attempts
Addressing Outdated Security Approaches
Despite advances in cybersecurity, many organizations continue using ineffective practices. An examination of ten outdated security practices people still swear by reveals common misconceptions that network security firms must overcome when working with new clients.
Relying solely on antivirus software represents perhaps the most dangerous outdated practice. Modern threats bypass traditional signature-based detection through polymorphic code, zero-day exploits, and fileless attacks. Professional security firms layer multiple detection methods including behavioral analysis, sandboxing, and threat intelligence feeds.
Password complexity requirements without length requirements create weak credentials. Research demonstrates that length matters far more than character variety. Network security firms implement policies requiring minimum 12-character passwords while encouraging passphrases that users can remember without writing down.
Modern Security Alternatives
| Outdated Practice | Modern Alternative | Benefit |
|---|---|---|
| Annual password changes | Breach-triggered resets + MFA | Reduces weak password creation |
| Perimeter-only defense | Zero-trust architecture | Assumes breach and verifies continuously |
| Manual patch management | Automated patch deployment | Closes vulnerabilities faster |
| Static security assessments | Continuous vulnerability scanning | Identifies new risks immediately |
The shift from reactive to proactive security defines modern network security firms. Rather than responding after breaches occur, these providers continuously hunt for threats, test defenses, and update controls based on emerging intelligence.
Comprehensive Best Practices for 2026
Current guidance from multiple sources, including network security best practices from Clouddle and enterprise-grade protection strategies from Soraxus, emphasizes several critical areas that network security firms prioritize for their clients.
Network Monitoring and Incident Response
Continuous monitoring forms the backbone of effective security operations. Network security firms deploy SIEM platforms that aggregate logs from all security devices, servers, and applications. Security analysts review alerts, investigate anomalies, and respond to confirmed incidents.
An effective incident response plan includes clearly defined roles, communication protocols, containment procedures, and recovery steps. Small businesses benefit tremendously from the expertise network security firms bring to incident handling, as most lack dedicated security staff with crisis management experience.
The plan should address:
- Initial detection and alert validation
- Containment to prevent further damage
- Evidence preservation for forensic analysis
- Threat eradication from all affected systems
- System restoration and verification
- Post-incident review and lessons learned
Regular tabletop exercises test these procedures without the pressure of an actual breach. Network security firms facilitate these exercises, identifying gaps and refining responses before real incidents occur.
Data Protection and Backup Security
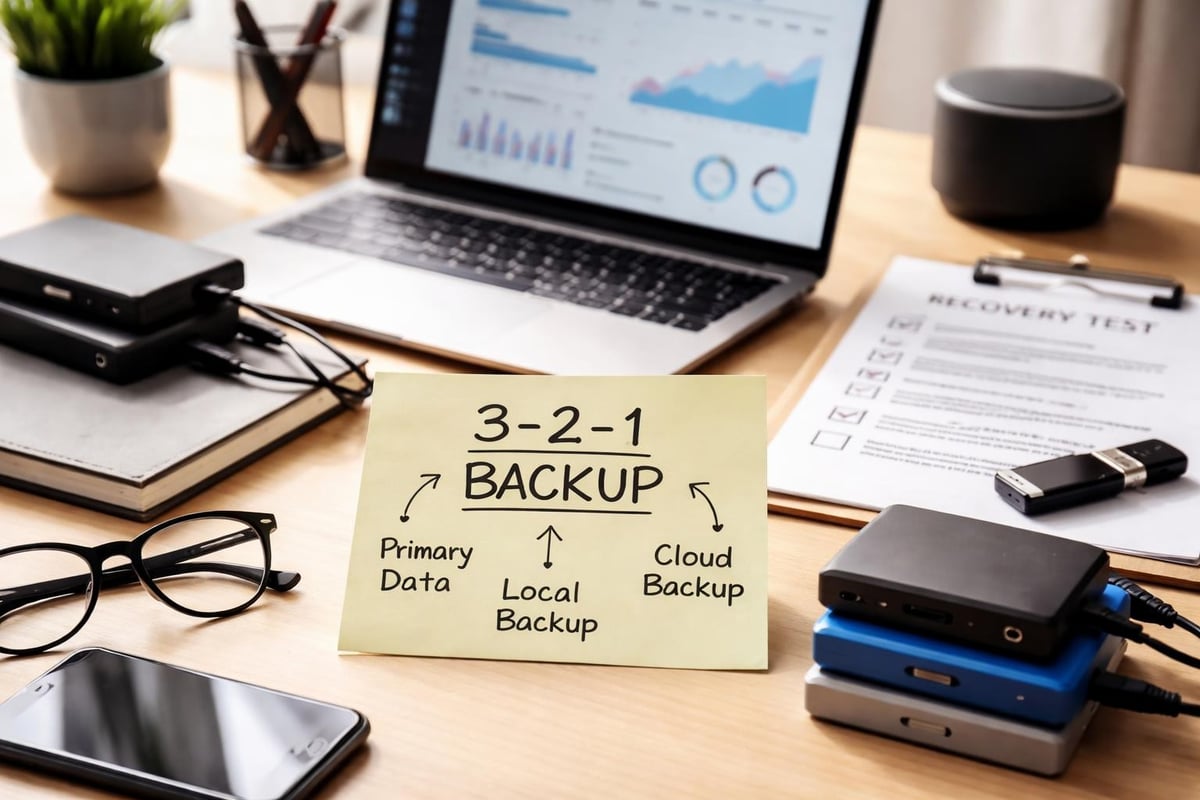
Network security extends to data protection strategies that ensure business continuity even after successful attacks. The 3-2-1 backup rule (three copies, two different media, one off-site) provides foundational protection, but network security firms enhance this with immutable backups that ransomware cannot encrypt.
Backup verification often gets overlooked until recovery fails. Professional firms regularly test restoration procedures, ensuring backups are complete, accessible, and functional. This proactive approach prevents discovering backup failures during emergencies when time is critical.
Integration with Managed IT Services
Network security firms increasingly operate as part of comprehensive managed service provider (MSP) offerings. This integration creates synergies where security considerations inform infrastructure decisions and operational practices enhance security posture.
For small businesses, working with a provider that combines managed IT services with security expertise eliminates coordination challenges between separate vendors. When one team handles both network operations and security, response times improve and accountability becomes clear.
The Fixed-Rate Advantage
Predictable security costs enable better budget planning. Network security firms offering fixed-rate pricing eliminate surprise expenses while providing comprehensive protection. This model aligns provider incentives with client success, as the firm's profitability depends on preventing incidents rather than billing for remediation.
Monthly or quarterly security reviews included in fixed-rate arrangements keep businesses informed about their security posture. These reviews cover recent threats, control effectiveness, compliance status, and recommendations for improvements.
Cloud Security Considerations
As businesses migrate to cloud platforms, network security firms adapt their approaches to hybrid and multi-cloud environments. Traditional perimeter-focused security gives way to identity-centric models that secure access regardless of location.
Cloud security requires attention to:
- Shared responsibility models that clarify provider versus customer obligations
- Cloud access security brokers (CASB) that enforce policies across cloud applications
- Configuration management to prevent insecure cloud resource deployment
- Data encryption both in transit and at rest
- API security protecting programmatic access to cloud services
Network security firms with cloud expertise help small businesses navigate these complexities, implementing appropriate controls without hindering the agility and scalability that motivate cloud adoption.
Compliance and Regulatory Requirements
Many industries face specific security regulations that network security firms help clients satisfy. HIPAA for healthcare, PCI DSS for payment processing, and various privacy laws impose technical and procedural requirements.
Compliance failures result in substantial fines, legal liability, and reputational damage. Professional security firms maintain current knowledge of regulatory requirements and implement necessary controls as part of their standard service delivery.
Training and Security Awareness
Technical controls alone cannot prevent all security incidents. Human error remains a leading cause of breaches, making employee training essential. Network security firms provide security awareness programs that teach staff to recognize phishing attempts, social engineering tactics, and suspicious activity.
Effective training programs include multiple components:
- Initial orientation for new employees
- Quarterly refresher sessions on current threats
- Simulated phishing campaigns to test awareness
- Role-specific training for employees with elevated privileges
- Incident reporting procedures and expectations
Measuring training effectiveness through metrics like phishing simulation click rates helps identify areas requiring additional attention. Network security firms track these metrics and adjust programs accordingly.
Vendor and Third-Party Risk Management
Small businesses increasingly rely on vendors, contractors, and partners who access their networks or handle sensitive data. Each connection creates potential security gaps that network security firms must address through vendor risk management programs.
Due diligence assessments evaluate vendor security postures before granting access. Ongoing monitoring ensures vendors maintain adequate controls throughout the relationship. Contractual requirements establish security expectations and liability for breaches.
| Risk Level | Assessment Frequency | Required Controls |
|---|---|---|
| High (direct data access) | Quarterly | SOC 2, encryption, MFA, audit rights |
| Medium (limited access) | Semi-annually | Security questionnaire, insurance |
| Low (no data access) | Annually | Basic security confirmation |
Network security firms streamline vendor assessments through standardized questionnaires, automated monitoring, and centralized risk tracking.
Emerging Technologies and Future Trends
Artificial intelligence and machine learning increasingly enhance threat detection capabilities. Network security firms deploy AI-powered tools that identify anomalous behavior patterns humans might miss. These technologies complement rather than replace human expertise, improving analyst efficiency.
Zero-trust architecture represents the future direction for network security. This model assumes no user or device is trustworthy by default, requiring continuous verification regardless of location. Implementation requires significant architectural changes that network security firms guide clients through methodically.
The Internet of Things (IoT) expands attack surfaces as businesses deploy smart devices throughout their operations. Each connected device represents a potential entry point requiring security controls. Network security firms help clients inventory IoT devices, segment them from critical systems, and monitor for compromise.
Protecting your business network requires expertise, vigilance, and resources that many small organizations struggle to maintain internally. As threats continue evolving and regulatory requirements expand, partnering with experienced professionals becomes increasingly essential for maintaining secure, compliant operations. Delphi Systems Inc. delivers comprehensive managed IT services with integrated cybersecurity for businesses throughout Lethbridge and surrounding areas, combining proactive monitoring, expert support, and predictable pricing to keep your network secure while you focus on growing your business.





