Small businesses increasingly rely on cloud infrastructure to store sensitive information, manage operations, and serve customers. While cloud platforms offer scalability and cost-effectiveness, they introduce unique security challenges that require careful consideration. Understanding how to protect your organization's data in cloud environments has become essential for maintaining customer trust, meeting regulatory requirements, and ensuring business continuity. Data security in cloud computing encompasses multiple layers of protection, from encryption and access controls to monitoring and compliance frameworks that work together to safeguard your most valuable digital assets.
Understanding Cloud Security Architecture
Cloud computing operates on a shared responsibility model where security obligations are distributed between the cloud service provider and the customer organization. Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service (SaaS) each present different security boundaries.
With IaaS solutions, businesses maintain responsibility for securing their operating systems, applications, and data while the provider secures the physical infrastructure. PaaS shifts more security responsibilities to the provider, but organizations still control their applications and data. SaaS platforms handle the majority of security tasks, though customers remain accountable for user access management and data governance.
Key Components of Cloud Security
Effective data security in cloud computing requires multiple defensive layers working in concert:
- Identity and access management controls who can view, modify, or delete information
- Encryption protocols protect data both in transit and at rest
- Network security measures prevent unauthorized access and detect intrusions
- Monitoring systems track user activity and identify anomalous behavior
- Backup and recovery solutions ensure data availability after incidents

The comprehensive discussion on data security and privacy in cloud computing highlights emerging research trends that shape how organizations approach these challenges. Understanding these foundations helps businesses make informed decisions about cloud adoption.
Encryption Strategies for Cloud-Based Data
Encryption transforms readable information into coded text that becomes useless to unauthorized parties. This fundamental security measure protects data during transmission over networks and while stored on cloud servers.
Organizations should implement encryption at multiple points in their cloud infrastructure. Data should be encrypted before leaving local systems, remain encrypted during transmission, and stay encrypted on cloud storage systems. This approach, known as end-to-end encryption, ensures that even if attackers intercept data or compromise cloud servers, they cannot access the actual information.
Encryption Key Management
Managing encryption keys presents one of the most critical challenges in cloud security. Businesses must decide whether to control their own keys or allow cloud providers to manage them.
| Approach | Advantages | Considerations |
|---|---|---|
| Customer-managed keys | Complete control over access, easier compliance demonstration | Requires technical expertise, risk of key loss |
| Provider-managed keys | Simplified operations, integrated with cloud services | Less control, potential compliance concerns |
| Hybrid model | Balance of control and convenience | More complex implementation |
Regardless of approach, organizations should implement strict key rotation policies, maintain secure backups of encryption keys, and enforce separation of duties to prevent unauthorized key access. The data security issues in cloud computing emphasize these practices as essential for maintaining data confidentiality and integrity.
Access Control and Identity Management
Controlling who can access cloud resources forms the foundation of data security in cloud computing. Implementing robust identity and access management (IAM) systems prevents unauthorized users from viewing or manipulating sensitive business information.
Modern IAM frameworks operate on the principle of least privilege, granting users only the minimum access necessary to perform their job functions. This approach limits the potential damage from compromised credentials or insider threats.
Multi-Factor Authentication Implementation
Single passwords no longer provide adequate protection for cloud resources. Multi-factor authentication (MFA) requires users to provide two or more verification factors:
- Something they know (password or PIN)
- Something they have (smartphone, hardware token, or smart card)
- Something they are (fingerprint, facial recognition, or other biometric)
Implementing MFA across all cloud access points dramatically reduces the risk of unauthorized access. Even if attackers steal passwords through phishing or data breaches, they cannot access systems without the additional authentication factors.
Role-based access control (RBAC) further enhances security by organizing permissions around job functions rather than individuals. When employees change positions or leave the organization, administrators simply adjust their role assignments rather than manually updating dozens of individual permissions.
Compliance and Regulatory Requirements
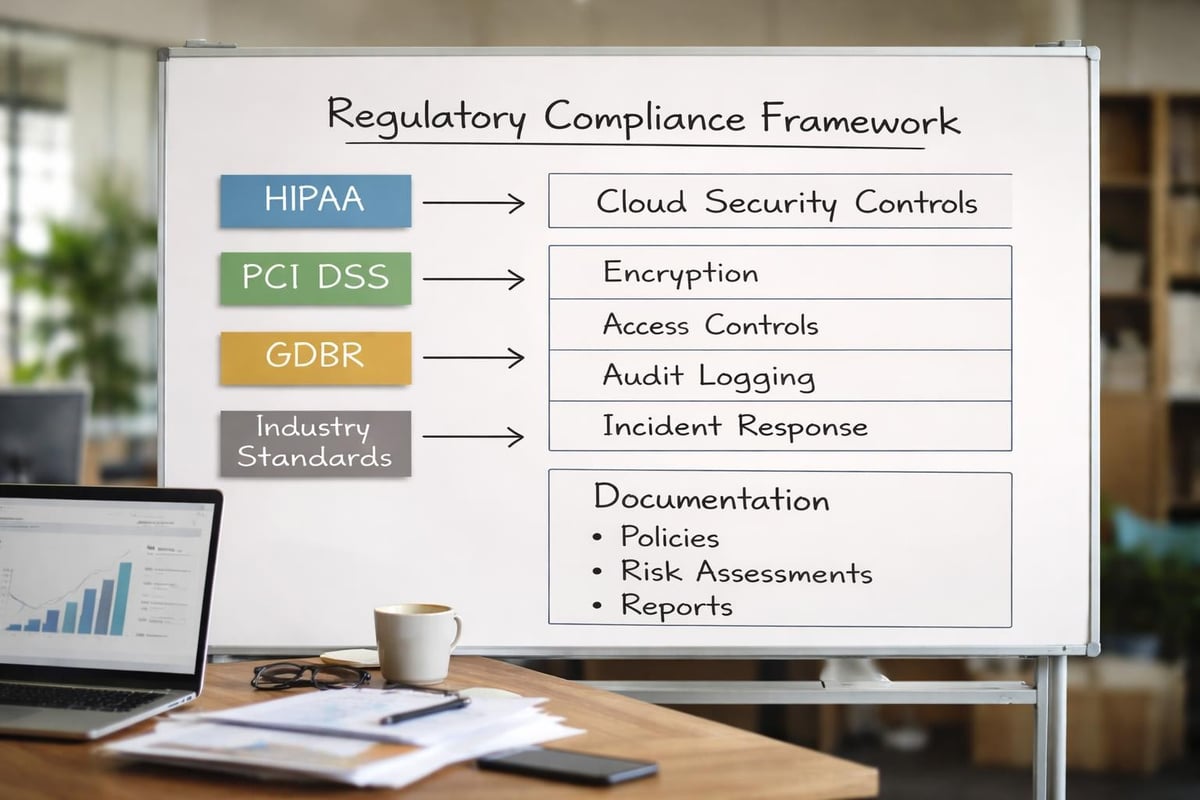
Businesses operating in cloud environments must navigate complex regulatory landscapes that govern data protection. Different industries face specific compliance requirements that affect how they secure and manage information.
Healthcare organizations must comply with HIPAA regulations protecting patient information. Financial institutions face requirements from PCI DSS for payment card data and various banking regulations. Even general businesses must address privacy laws like GDPR for European customers or CCPA for California residents.
Security Standards and Certifications
Cloud providers offer various certifications demonstrating their commitment to security standards. Organizations should verify that their cloud partners maintain relevant certifications:
- SOC 2 Type II reports validate security controls over extended periods
- ISO 27001 certification demonstrates comprehensive information security management
- FedRAMP authorization indicates government-grade security for federal data
- Multi-Tier Cloud Security standard provides structured security levels for different data sensitivity
Documentation requirements constitute a significant compliance burden. Businesses must maintain detailed records of security policies, access logs, configuration changes, and incident responses. Automated compliance monitoring tools help organizations track these requirements and generate necessary reports.
Data Backup and Disaster Recovery
Cloud infrastructure provides excellent opportunities for implementing robust backup and disaster recovery strategies. However, relying solely on cloud providers for data protection can create vulnerabilities.
The 3-2-1 backup rule remains relevant in cloud environments: maintain three copies of data, store them on two different media types, and keep one copy offsite. In cloud contexts, this might mean primary data on cloud servers, a backup on different cloud infrastructure, and an additional copy on local systems or a separate cloud region.
Recovery Time and Point Objectives
Organizations must define their tolerance for downtime and data loss:
Recovery Time Objective (RTO) specifies the maximum acceptable downtime after an incident. A four-hour RTO means systems must return to operation within four hours of failure.
Recovery Point Objective (RPO) determines the maximum acceptable data loss measured in time. A one-hour RPO requires backups frequent enough that no more than one hour of data becomes unrecoverable.
These objectives drive decisions about backup frequency, infrastructure redundancy, and recovery procedures. Businesses with stringent RTOs and RPOs require real-time replication and automated failover systems, while those with more flexibility can use scheduled backups and manual recovery processes.
Testing recovery procedures regularly ensures they work when needed. Many organizations discover backup failures only when attempting recovery during actual emergencies. Quarterly or monthly recovery drills validate backup integrity and train staff on recovery procedures.
Network Security in Cloud Environments
Protecting the network perimeter in cloud computing requires different approaches than traditional on-premises infrastructure. Cloud networks are software-defined, providing both opportunities and challenges for security implementation.
Virtual Private Networks (VPNs) create encrypted tunnels between local networks and cloud resources, preventing eavesdropping on data transmissions. However, VPNs alone do not protect against threats originating within cloud environments.
Microsegmentation and Zero Trust
Modern cloud security increasingly adopts zero trust principles that assume no user or system is inherently trustworthy. Rather than protecting only the network perimeter, zero trust architectures verify every access request regardless of origin.
Microsegmentation divides cloud networks into isolated segments with granular security controls. Rather than allowing broad access across cloud infrastructure, microsegmentation restricts lateral movement by attackers who compromise one system.
The Certificate of Competence in Zero Trust demonstrates the growing importance of these concepts in cloud security training. Organizations implementing these approaches significantly reduce their attack surface and limit potential breach impact.
Network monitoring tools track traffic patterns, identify anomalies, and detect potential intrusions. Modern solutions use machine learning to establish baseline behavior patterns and alert administrators to deviations that might indicate security incidents.
Securing Data in Transit and at Rest
Data security in cloud computing requires protection during two distinct states. Data in transit moves between locations across networks, while data at rest resides on storage systems.
Transport Layer Security (TLS) protocols encrypt data moving between users and cloud services. Modern implementations should use TLS 1.2 or newer, as older versions contain known vulnerabilities. Certificate validation ensures users connect to legitimate services rather than imposter sites operated by attackers.
API security deserves special attention as applications increasingly communicate through application programming interfaces. API keys, OAuth tokens, and other authentication mechanisms must be properly secured to prevent unauthorized access to cloud services.
Storage Security Measures
Cloud storage security extends beyond encryption to include access logging, versioning, and retention policies. Organizations should implement:
- Access logging to track who views or modifies stored data
- Versioning to maintain historical copies and recover from accidental changes
- Lifecycle policies to automatically archive or delete data based on age
- Geographic restrictions to ensure data stays in specific jurisdictions
Data masking strategies offer additional protection by obscuring sensitive information in non-production environments. Development and testing teams can work with realistic data structures without exposing actual customer information.
Vendor Security Assessment
Selecting cloud service providers requires thorough security evaluation. Not all providers offer equivalent protection, and security failures by vendors directly impact their customers.
Organizations should review provider security certifications, audit reports, and compliance documentation. Third-party security assessments provide independent validation of provider claims. The overview of cloud computing security details various security controls and compliance issues that should factor into vendor selection.
Service Level Agreements
Service Level Agreements (SLAs) define provider commitments regarding availability, performance, and security. Businesses should carefully review:
| SLA Component | Key Considerations |
|---|---|
| Uptime guarantees | Percentage uptime, calculation methods, credit compensation |
| Security incident notification | Timeline for breach notification, information provided |
| Data ownership | Rights to data, portability provisions, deletion guarantees |
| Support response times | Availability of security expertise, escalation procedures |
Understanding provider responsibilities helps organizations identify gaps they must address through additional security measures or third-party tools.

Employee Training and Security Awareness
Human error remains a leading cause of cloud security incidents. Employees who lack security awareness may fall victim to phishing attacks, misconfigure cloud services, or inadvertently expose sensitive data.
Comprehensive security training should cover cloud-specific risks including credential management, data sharing practices, and recognizing social engineering attempts. Training programs work best when delivered regularly rather than as one-time events, as security threats constantly evolve.
Simulated phishing exercises help identify employees who need additional training while reinforcing security awareness across the organization. These exercises should focus on education rather than punishment to encourage reporting of actual security incidents.
Clear policies governing cloud usage prevent well-intentioned employees from creating security vulnerabilities. Policies should address approved cloud services, data classification requirements, and procedures for reporting suspicious activity. When businesses establish clear guidelines, employees can make secure decisions without constant management oversight.
Monitoring and Incident Response
Continuous monitoring detects security incidents before they escalate into major breaches. Cloud environments generate massive volumes of log data that security teams must analyze to identify threats.
Security Information and Event Management (SIEM) systems aggregate logs from multiple sources, correlate events, and highlight potential security incidents. Modern SIEM solutions incorporate threat intelligence feeds that identify known attack patterns and malicious IP addresses.
Developing an Incident Response Plan
Every organization needs a documented incident response plan that outlines steps to take when security incidents occur:
- Detection and analysis to confirm incidents and assess their scope
- Containment to prevent further damage or data loss
- Eradication to remove threats from affected systems
- Recovery to restore normal operations
- Lessons learned to improve security posture
Response plans should identify team members responsible for different tasks, establish communication protocols, and define escalation criteria. Regular tabletop exercises test plan effectiveness and familiarize team members with their roles.
Post-incident reviews identify security gaps and process improvements. Organizations that learn from incidents strengthen their defenses against future attacks.
Cloud Security for Small Businesses
Small businesses face unique challenges implementing data security in cloud computing. Limited IT budgets and staff require strategic approaches that maximize protection without overwhelming resources.
Managed service providers offer expertise and tools that would be cost-prohibitive to develop internally. These partnerships give small businesses access to enterprise-grade security capabilities through predictable monthly fees.
Cloud-native security tools often provide better value than traditional enterprise security products. Major cloud providers offer built-in security features included in their base pricing, reducing the need for expensive third-party solutions.
Automation reduces the burden on small IT teams by handling routine security tasks. Automated patch management, backup scheduling, and security scanning ensure consistent protection without constant manual intervention. According to cloud computing statistics, businesses increasingly rely on automated security tools to address the growing complexity of cloud environments.
Starting with foundational security measures and expanding over time creates a practical roadmap for small businesses. Prioritizing encryption, access controls, and backup systems addresses the most critical risks before investing in advanced security capabilities.
Protecting business data in cloud environments requires comprehensive strategies spanning encryption, access controls, compliance, and continuous monitoring. Small businesses in Lethbridge and surrounding areas need security expertise without the overhead of maintaining full-time security teams. Delphi Systems Inc. provides managed IT services that implement these security best practices, monitor your cloud infrastructure, and ensure your data remains protected while you focus on growing your business.





