Modern businesses face unprecedented cybersecurity challenges as digital transformation accelerates and threat actors become increasingly sophisticated. Small businesses in Lethbridge and across Canada are particularly vulnerable, often lacking the internal resources to maintain comprehensive security protocols. It security management services provide a strategic solution by delivering expert oversight, proactive monitoring, and rapid incident response that keeps business operations secure and compliant. These managed services transform security from a reactive burden into a strategic advantage, allowing organizations to focus on growth while professionals handle the complex task of protecting digital assets.
Understanding IT Security Management Services
It security management services encompass a comprehensive approach to protecting an organization's information systems, data, and network infrastructure. Rather than simply installing antivirus software and hoping for the best, these services implement layered defense strategies that address vulnerabilities across multiple dimensions.
Professional security management begins with a thorough assessment of existing infrastructure, identifying weak points in networks, applications, and user access protocols. This evaluation forms the foundation for a customized security framework aligned with business objectives and regulatory requirements.
The scope of it security management services typically includes:
- 24/7 network monitoring to detect anomalous activities and potential breaches
- Access control management ensuring only authorized personnel access sensitive systems
- Patch management keeping all software and systems updated against known vulnerabilities
- Security policy development establishing clear protocols for data handling and system use
- Incident response planning preparing systematic procedures for addressing security events
- Compliance management ensuring adherence to industry regulations and standards

The Evolution of Security Threats
Cybersecurity threats have evolved dramatically over the past decade. Today's attackers employ sophisticated techniques including ransomware, phishing campaigns, and advanced persistent threats that traditional security measures cannot adequately address.
Small businesses often mistakenly believe they're too small to attract cybercriminal attention. Statistics prove otherwise, with over 43% of cyberattacks targeting small businesses. These organizations present attractive targets precisely because they typically maintain fewer security resources than larger enterprises.
Modern it security management services address this reality by implementing enterprise-grade protection adapted for smaller organizational scales and budgets. Managed service providers leverage economies of scale, offering access to advanced security tools and expertise that would be prohibitively expensive for individual small businesses to maintain internally.
Core Components of Effective Security Management
Comprehensive information security management requires coordinated attention across multiple operational areas. Each component plays a distinct role in the overall security posture.
Threat Detection and Prevention
Real-time monitoring forms the frontline defense against security incidents. Advanced security information and event management (SIEM) systems collect and analyze data from across the network, identifying patterns that indicate potential threats.
It security management services deploy sophisticated tools that correlate events from firewalls, servers, workstations, and cloud applications. This holistic view enables rapid identification of coordinated attacks that might appear innocuous when examining individual systems in isolation.
Prevention mechanisms include:
- Next-generation firewalls that inspect traffic at the application layer
- Intrusion detection and prevention systems blocking suspicious activities
- Email security gateways filtering phishing attempts and malicious attachments
- Endpoint protection securing individual devices against malware and exploits
- Web filtering preventing access to known malicious sites
Access Control and Identity Management
Controlling who accesses what resources represents a critical security function. Automated provisioning systems streamline the process of granting and revoking access privileges based on user roles and responsibilities.
Effective it security management services implement the principle of least privilege, ensuring users only access systems and data necessary for their specific job functions. This approach dramatically reduces the potential damage from compromised credentials or insider threats.
| Access Control Method | Security Benefit | Implementation Complexity |
|---|---|---|
| Multi-factor Authentication | High – blocks 99.9% of automated attacks | Low – easy to deploy |
| Role-based Access Control | Medium – limits lateral movement | Medium – requires planning |
| Single Sign-On | Medium – reduces password fatigue | Medium – integration required |
| Privileged Access Management | High – protects administrative accounts | High – ongoing maintenance |
Vulnerability Assessment and Patch Management
Software vulnerabilities provide common entry points for cyberattacks. New vulnerabilities emerge constantly, requiring systematic approaches to identification and remediation.
Professional it security management services conduct regular vulnerability scans across all network assets, prioritizing discovered issues based on severity and exploitability. This proactive approach identifies weaknesses before attackers can exploit them.
Patch management ensures timely application of security updates across operating systems, applications, and firmware. Automated deployment tools apply critical patches during maintenance windows, minimizing disruption while maintaining security.
Risk Management and Compliance
IT risk management provides the strategic framework for security decision-making. Rather than attempting to eliminate all risks, which is both impossible and economically impractical, organizations must identify, assess, and prioritize risks based on potential business impact.
Risk Assessment Methodology
Effective risk assessment follows a structured process:
- Asset identification cataloging all systems, applications, and data
- Threat identification determining potential attack vectors and scenarios
- Vulnerability analysis evaluating weaknesses in current defenses
- Impact assessment calculating potential business consequences
- Risk prioritization ranking threats by likelihood and severity
It security management services bring experienced professionals who conduct these assessments using established frameworks and industry best practices. Their external perspective often identifies blind spots that internal teams overlook due to familiarity with existing systems.

Regulatory Compliance Requirements
Depending on industry and operations, businesses may face various regulatory requirements governing data protection and privacy. Canadian organizations handling personal information must comply with PIPEDA (Personal Information Protection and Electronic Documents Act).
Healthcare organizations face additional requirements under provincial health information acts. Financial services firms must address sector-specific regulations. Even businesses without explicit regulatory obligations should consider implementing ITIL security management frameworks based on ISO 27001 standards.
It security management services help navigate this complex regulatory landscape by:
- Interpreting regulatory requirements and translating them into technical controls
- Implementing necessary security measures to demonstrate compliance
- Maintaining documentation proving adherence to standards
- Conducting periodic audits to verify ongoing compliance
- Updating procedures as regulations evolve
Incident Response and Business Continuity
Despite best preventive efforts, security incidents remain inevitable. The difference between minor disruptions and catastrophic breaches often lies in the speed and effectiveness of incident response.
Structured Incident Response
Professional it security management services maintain detailed incident response plans covering detection, containment, eradication, and recovery phases. These plans define clear roles, communication protocols, and decision-making authority to eliminate confusion during high-stress situations.
Detection phase activities include monitoring alerts, investigating suspicious activities, and determining whether an actual security incident has occurred. False positives waste resources, while missed detections allow attacks to progress.
Containment strategies limit damage by isolating affected systems, blocking malicious communications, and preventing lateral movement within networks. It security management services implement both short-term containment measures for immediate threat suppression and long-term solutions addressing root causes.
Eradication procedures remove malicious code, close exploited vulnerabilities, and verify that attackers no longer maintain access. This phase requires thorough analysis to ensure complete removal rather than superficial remediation that allows attacks to resume.
Recovery operations restore affected systems to normal operation, validate data integrity, and resume business processes. It security management services coordinate these efforts to minimize downtime while ensuring security.
Data Backup and Disaster Recovery
Ransomware attacks and data breaches underscore the critical importance of comprehensive backup strategies. Effective data protection follows the 3-2-1 rule: three copies of data, on two different media types, with one copy stored offsite.
Modern it security management services implement sophisticated backup solutions including:
- Continuous data protection capturing changes in real-time
- Immutable backups preventing ransomware from encrypting backup copies
- Geographic redundancy storing copies in multiple physical locations
- Regular restoration testing verifying backup integrity and recovery procedures
- Automated backup monitoring alerting to failed or incomplete backups
| Backup Strategy | Recovery Time Objective | Recovery Point Objective | Cost Level |
|---|---|---|---|
| Daily Full Backups | 24-48 hours | Up to 24 hours | Low |
| Incremental with Weekly Full | 12-24 hours | Up to 1 hour | Medium |
| Continuous Replication | 1-4 hours | Minutes | High |
| High Availability Clustering | Minutes | Near-zero | Very High |
Selecting IT Security Management Services
Choosing the right security partner significantly impacts both protection effectiveness and budget efficiency. Small businesses should evaluate providers based on several critical criteria.
Service Scope and Capabilities
Not all it security management services offer identical capabilities. Some providers focus primarily on monitoring and alerting, while others deliver comprehensive managed security including active threat hunting, forensic analysis, and remediation services.
Businesses should clearly define their security requirements before evaluating providers. Consider factors including:
- Current security maturity level and existing infrastructure
- Industry-specific compliance requirements
- Budget constraints and acceptable investment levels
- Internal IT capabilities and desired service division
- Growth projections and scalability needs
The most expensive provider isn't necessarily the best fit. Optimal selection balances comprehensive protection with practical business needs and financial realities.
Response Times and Support Availability
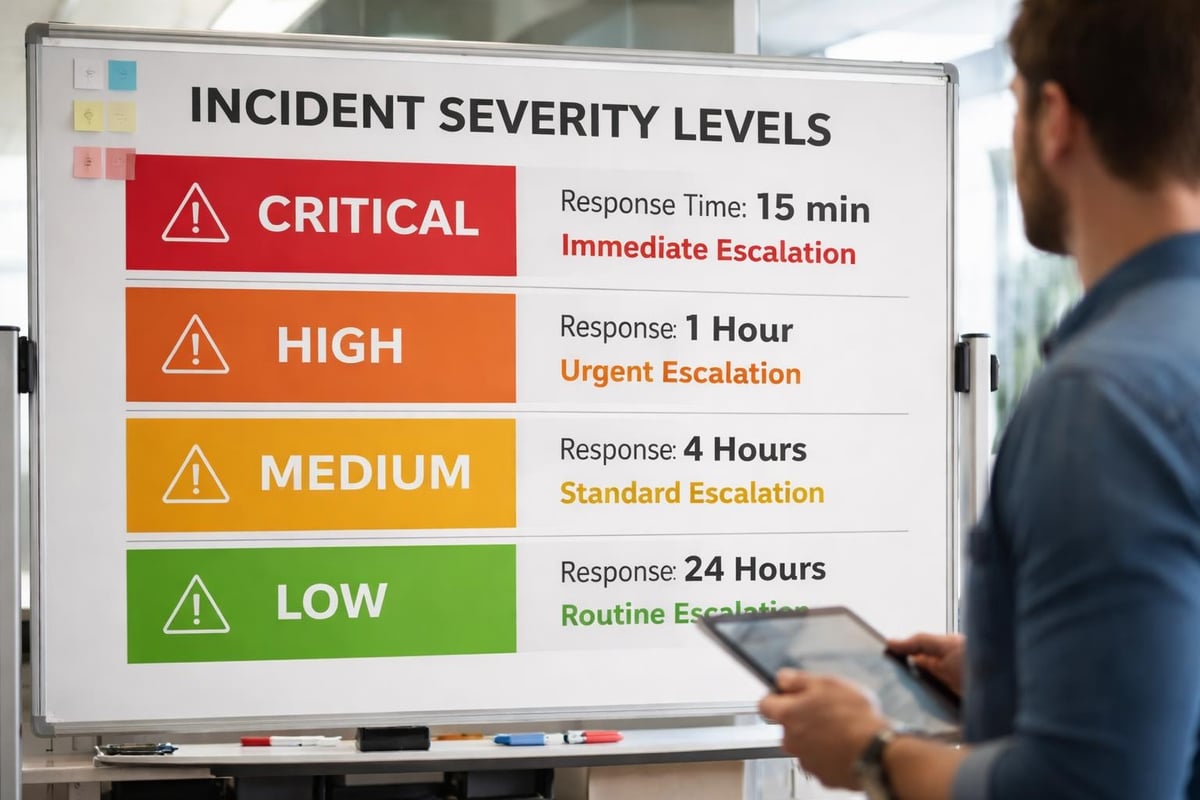
Security incidents don't respect business hours. Effective it security management services provide 24/7 monitoring and rapid response capabilities. When evaluating providers, clarify specific response time commitments for different severity levels.
Critical incidents require immediate attention, ideally within 15-30 minutes. Less urgent issues might warrant response times measured in hours rather than minutes. Ensure service level agreements clearly define these expectations and associated penalties for non-compliance.
Transparency and Communication
Security operations require ongoing collaboration between service providers and client organizations. Effective it security management services maintain transparent communication regarding:
- Security posture reporting regular summaries of threat landscape and defensive effectiveness
- Incident notifications timely alerts regarding detected threats and ongoing investigations
- Remediation recommendations actionable guidance for addressing identified vulnerabilities
- Strategic planning periodic consultations regarding security roadmap and investment priorities
Providers should deliver reports in accessible language that business leaders can understand, not just technical jargon comprehensible only to IT specialists. Security exists to protect business objectives, and communication should reflect this business-centric perspective.
Cost Structures and Investment Considerations
Understanding pricing models helps businesses budget appropriately for it security management services and evaluate provider proposals effectively.
Fixed-Rate versus Variable Pricing
Many managed service providers offer fixed monthly rates covering defined service scopes. This predictable pricing simplifies budgeting and eliminates surprise expenses. Fixed-rate models work well for stable environments with consistent security requirements.
Variable pricing ties costs to actual resource consumption or service utilization. This approach can provide flexibility for businesses with fluctuating needs, though it introduces budget uncertainty.
For small businesses, fixed-rate structures typically offer superior value and financial predictability. They allow providers to invest in automation and efficiency improvements that benefit both parties over time.
Total Cost of Ownership Analysis
When evaluating it security management services, compare total costs against alternative approaches. Building internal security capabilities requires:
- Personnel expenses including salaries, benefits, and ongoing training for security specialists
- Technology investments purchasing security tools, monitoring systems, and infrastructure
- Operational overhead maintaining 24/7 coverage through shift staffing
- Opportunity costs diverting attention from core business activities
| Cost Component | Internal Security Team | Managed Security Services |
|---|---|---|
| Annual Personnel | $120,000 – $180,000 | Included in service fee |
| Security Tools | $15,000 – $40,000 | Included in service fee |
| Training and Certification | $5,000 – $10,000 | Included in service fee |
| 24/7 Coverage | Requires multiple staff | Included in service fee |
| Typical Total Annual Cost | $150,000 – $250,000+ | $24,000 – $72,000 |
These figures demonstrate why it security management services deliver exceptional value for small and medium businesses lacking resources for comprehensive internal security programs.
Integration with Broader IT Management
Security doesn't exist in isolation but integrates with broader information security infrastructure and operational processes. Effective it security management services coordinate seamlessly with other IT functions.
Cloud Security Management
Cloud computing introduces unique security considerations distinct from traditional on-premises infrastructure. Shared responsibility models divide security obligations between cloud providers and customers, with specific boundaries varying by service type.
Infrastructure as a Service (IaaS) requires customers to secure operating systems, applications, and data. Platform as a Service (PaaS) shifts some responsibilities to providers. Software as a Service (SaaS) delivers maximum provider responsibility, though customers still must configure security settings appropriately.
It security management services help navigate these complexities by:
- Configuring cloud security controls according to best practices
- Monitoring cloud environments for misconfigurations and threats
- Managing identity and access across hybrid environments
- Ensuring data encryption in transit and at rest
- Implementing cloud-specific backup and recovery strategies
Network Performance and Security Balance
Security measures can impact network performance if implemented carelessly. Deep packet inspection, encryption processing, and security scanning consume computational resources and introduce latency.
Professional it security management services architect solutions balancing protection requirements with performance needs. Modern security appliances incorporate dedicated processing hardware accelerating security functions without degrading throughput.
Regular performance monitoring identifies bottlenecks and optimization opportunities. Security should enhance business operations by preventing disruptions, not create new performance problems through excessive overhead.
Training and Security Awareness
Technology addresses only part of the security equation. Human factors remain critical, as employees often represent both the greatest vulnerability and most important defense layer.
Employee Security Training Programs
Effective it security management services include comprehensive security awareness training covering:
- Phishing recognition identifying suspicious emails and messages
- Password hygiene creating strong passwords and using password managers
- Physical security protecting devices and preventing unauthorized access
- Social engineering recognizing manipulation attempts
- Incident reporting knowing how and when to report security concerns
Training should occur regularly, not just during onboarding. Quarterly refreshers maintain awareness and address emerging threat vectors. Simulated phishing campaigns test employee vigilance and identify individuals requiring additional training.
Security Policy Development and Enforcement
Clear policies establish expectations regarding acceptable use, data handling, and security procedures. It security management services help develop comprehensive policy frameworks covering:
- Acceptable use policies defining appropriate technology utilization
- Data classification schemes categorizing information by sensitivity
- Access control policies governing system and data permissions
- Incident response procedures detailing employee responsibilities during security events
- Remote work policies addressing home office security requirements
Policies must be communicated clearly, acknowledged formally, and enforced consistently. Regular reviews ensure policies remain current as business needs and threat landscapes evolve.
Future Trends in Security Management
The security landscape continues evolving rapidly, with emerging technologies and threats reshaping requirements for it security management services.
Artificial Intelligence and Machine Learning
AI-powered security tools analyze vast data volumes identifying patterns human analysts would miss. Machine learning algorithms detect anomalies indicating zero-day exploits or advanced persistent threats that signature-based detection cannot recognize.
It security management services increasingly incorporate these technologies, though human expertise remains essential for contextual analysis and strategic decision-making. The combination of AI efficiency with human judgment delivers optimal results.
Zero Trust Architecture
Traditional security models assumed internal networks were trustworthy, focusing defenses at network perimeters. Modern threats require abandoning this assumption in favor of zero trust approaches that verify every access request regardless of origin.
It security management services implement zero trust principles through:
- Continuous authentication and authorization
- Micro-segmentation limiting lateral movement
- Least privilege access controls
- Comprehensive logging and monitoring
- Encryption for all communications
This fundamental shift requires significant architectural changes but dramatically improves security posture against modern threats.
Security Automation and Orchestration
Manual security processes cannot keep pace with the volume and speed of modern attacks. Automation handles repetitive tasks including log analysis, threat intelligence correlation, and initial incident response.
Security orchestration platforms coordinate multiple security tools, enabling rapid automated responses to detected threats. It security management services leverage these capabilities to improve response times while reducing operational costs.
Protecting your business from cyber threats requires comprehensive strategies, advanced tools, and ongoing expertise that it security management services deliver efficiently and affordably. Small businesses gain enterprise-grade security without the overhead of building internal security teams, allowing them to compete confidently in an increasingly digital marketplace. Delphi Systems Inc. helps Lethbridge businesses implement robust security frameworks with fixed-rate pricing and 24/7 monitoring, ensuring your IT infrastructure remains secure while you focus on growing your business.





