Small businesses face an unprecedented array of digital threats in 2026, making robust protection essential for operational continuity and customer trust. The complexity of modern cyber threats demands a comprehensive approach that extends beyond simple antivirus software. As businesses in Lethbridge and across Canada increasingly rely on digital infrastructure, implementing effective strategies for cyber security has become a fundamental business requirement rather than an optional consideration. Understanding the evolving threat landscape and adopting proven frameworks helps organizations build resilient defenses that protect valuable data and maintain business continuity.
The Current Threat Landscape for Small Business Networks
The cybersecurity environment has grown significantly more sophisticated over the past year, with threat actors leveraging artificial intelligence and automation to scale their attacks. Small businesses often mistakenly believe they're too insignificant to attract attention, yet they represent attractive targets precisely because of their frequently limited security resources.
Ransomware attacks continue to dominate the threat landscape, with criminals demanding payment in exchange for decrypting essential business data. These attacks can paralyze operations for days or weeks, resulting in substantial revenue loss and reputational damage. Phishing campaigns have evolved beyond obvious spam emails into highly convincing messages that impersonate trusted vendors, partners, or even internal executives.
The World Economic Forum’s Global Cybersecurity Outlook 2025 highlights how geopolitical tensions and emerging technologies intensify the complexity businesses face when protecting their digital assets.
Common Vulnerabilities Exploited by Attackers
- Unpatched software and operating systems
- Weak or reused passwords across multiple systems
- Inadequate employee training on security awareness
- Unsecured remote access points
- Lack of multi-factor authentication
- Insufficient network segmentation
Organizations must recognize that cybersecurity isn't solely a technical challenge. Human error accounts for a significant portion of successful breaches, making employee education a critical component of any comprehensive security strategy.

Foundational Security Controls for Business Protection
Establishing baseline security controls provides the foundation for cyber security across organizations of all sizes. These fundamental practices create multiple defensive layers that significantly increase the difficulty and cost for attackers attempting to compromise systems.
The NIST Special Publication 800-53 offers a comprehensive catalog of security controls that organizations can implement based on their specific risk profiles and operational requirements. While this framework was originally designed for federal systems, its principles apply equally well to private sector organizations seeking structured guidance.
Essential Technical Controls
| Control Type | Implementation | Business Impact |
|---|---|---|
| Access Management | Multi-factor authentication, role-based permissions | Prevents unauthorized access to sensitive systems |
| Network Security | Firewalls, intrusion detection, VPN requirements | Blocks malicious traffic before it reaches critical assets |
| Data Protection | Encryption at rest and in transit, secure backups | Ensures data remains protected even if perimeter defenses fail |
| Endpoint Security | Antivirus, EDR solutions, patch management | Secures individual devices against malware and exploits |
Regular vulnerability assessments help identify weaknesses before attackers can exploit them. These assessments should include both automated scanning tools and periodic manual reviews by experienced security professionals who understand the specific context of your business operations.
Network Monitoring and Threat Detection
Continuous monitoring forms a critical defense mechanism for cyber security, enabling organizations to identify suspicious activity before it escalates into a full breach. Modern monitoring solutions analyze network traffic patterns, system logs, and user behavior to detect anomalies that might indicate an active attack or compromised account.
Many small businesses lack the resources to staff a 24/7 security operations center, making managed IT services an attractive solution. Professional monitoring services provide round-the-clock vigilance, with experienced analysts reviewing alerts and responding to potential incidents before they cause significant damage.
Key monitoring capabilities include:
- Real-time traffic analysis for unusual patterns
- Log aggregation from all critical systems
- Automated alert generation for suspicious activities
- Regular reporting on security events and trends
- Integration with threat intelligence feeds
The CISA best practices guidance emphasizes that comprehensive logging serves as both a detection mechanism and an essential tool for forensic investigation following security incidents.
Implementing effective monitoring requires careful configuration to balance security with operational efficiency. Too many false alerts lead to "alert fatigue," where legitimate threats get overlooked amid constant notifications about benign activities.
Data Backup and Recovery Planning
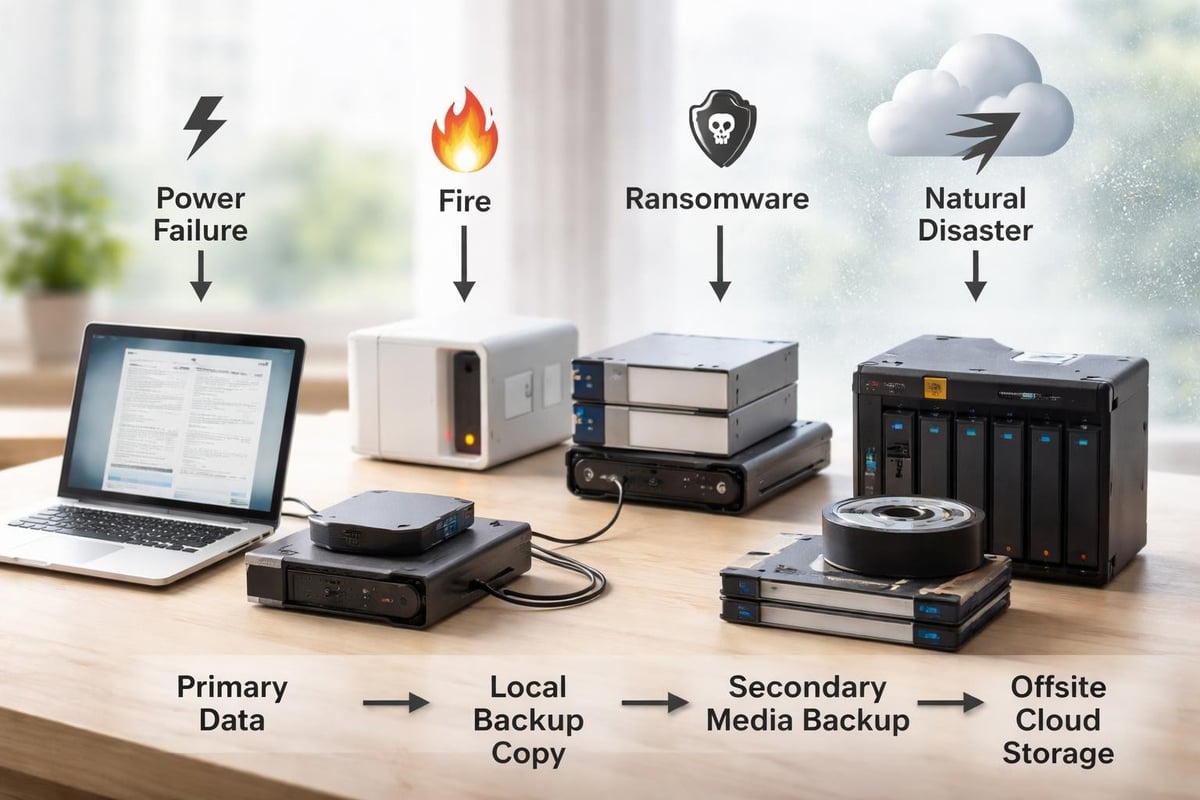
No defensive strategy is perfect, which makes comprehensive backup and recovery planning essential for cyber security resilience. Organizations must assume that eventually a breach, ransomware attack, or system failure will occur, making the ability to quickly restore operations from clean backups critically important.
The 3-2-1 Backup Rule
Modern backup strategies typically follow the 3-2-1 principle, which provides redundancy against various failure scenarios:
- Maintain three copies of critical data (one primary, two backups)
- Store backups on two different media types (disk, cloud, tape)
- Keep one backup copy offsite (separate physical location or cloud)
Testing backup restoration regularly ensures that backups actually work when needed. Many organizations discover too late that their backup processes were incomplete or corrupted, leaving them unable to recover from attacks. Schedule quarterly restoration tests using non-production environments to verify backup integrity.
Cloud-based backup solutions offer several advantages for small businesses, including automated scheduling, geographic redundancy, and scalability without significant infrastructure investment. However, organizations must ensure cloud backups maintain appropriate encryption and access controls to prevent attackers from compromising both production systems and backup repositories.
Emerging Trends Shaping Security Strategies
The cybersecurity landscape continues evolving rapidly, with new technologies and approaches reshaping how organizations protect their assets. Understanding these trends helps businesses make informed decisions about where to focus limited security resources.
Artificial intelligence plays an increasingly prominent role on both sides of the security equation. Defenders use AI to analyze vast amounts of data, identify patterns that humans might miss, and automate responses to common threats. Meanwhile, attackers leverage AI to create more convincing phishing messages, discover vulnerabilities faster, and adapt their tactics in real-time based on defensive responses.
According to ANSecurity’s analysis of 2025 trends, the adoption of Zero Trust Architecture represents a fundamental shift in how organizations approach network security. Rather than assuming everything inside the network perimeter is trustworthy, Zero Trust requires continuous verification for every user and device attempting to access resources.
Zero Trust Implementation Priorities
- Identity verification for all access requests
- Least-privilege access policies (minimum necessary permissions)
- Micro-segmentation of network resources
- Continuous monitoring and validation
- Encryption of all data flows
The NSA’s guidance on AI system security emphasizes protecting data integrity and implementing cryptographic measures as essential components for cyber security in AI-driven processes. As more business applications incorporate AI capabilities, these considerations become relevant even for small organizations that might not consider themselves AI adopters.
Employee Training and Security Awareness
Technology alone cannot solve security challenges when human error creates vulnerabilities that bypass even the most sophisticated technical controls. Comprehensive employee training transforms staff from potential security weaknesses into an effective defensive layer for cyber security.
Effective training programs go beyond annual compliance videos that employees click through without engagement. Instead, they create ongoing awareness through:
- Simulated phishing exercises that test employee vigilance
- Regular security updates about current threats targeting your industry
- Clear policies explaining acceptable use and security responsibilities
- Easy reporting mechanisms for suspicious activities
- Positive reinforcement when employees identify and report potential threats
New employees should receive security training during onboarding, establishing security awareness as a core component of organizational culture from day one. Refresher training should occur at least quarterly, with additional targeted sessions when new threats emerge or after security incidents.
Make reporting potential security issues psychologically safe. Employees who fear punishment for clicking a suspicious link will hide their mistakes rather than reporting them promptly, allowing attackers additional time to exploit compromised accounts.
Compliance Frameworks and Regulatory Requirements
Various industries face specific regulatory requirements for cyber security, making compliance an important consideration alongside general security best practices. Understanding applicable frameworks helps organizations meet legal obligations while implementing controls that genuinely enhance security rather than simply checking boxes.
| Framework | Primary Audience | Key Focus Areas |
|---|---|---|
| PCI DSS | Organizations handling payment cards | Payment data protection, network security |
| HIPAA | Healthcare providers and associates | Patient data privacy, access controls |
| PIPEDA | Canadian businesses handling personal data | Privacy rights, data protection |
| SOC 2 | Service providers | Security, availability, confidentiality controls |
Even organizations without specific regulatory requirements benefit from reviewing these frameworks, as they codify security practices developed through extensive industry experience. The controls they recommend address common vulnerabilities that affect businesses across all sectors.
Maintaining compliance documentation serves dual purposes: demonstrating regulatory adherence and providing evidence of due diligence should a breach occur. Courts and regulators view organizations more favorably when they can demonstrate systematic efforts to protect data, even if those efforts ultimately proved insufficient against a sophisticated attack.

Managed Security Services for Small Business
Small businesses frequently lack the expertise, resources, and time to implement comprehensive security programs internally. Managed IT service providers offer an effective solution for cyber security, delivering enterprise-grade protection at a fraction of the cost of building internal security teams.
Professional managed services typically include:
- Continuous network monitoring with 24/7 threat detection
- Patch management ensuring systems remain current
- Security tool management for firewalls, antivirus, and endpoint protection
- Incident response when security events occur
- Strategic planning aligned with business objectives
- Compliance assistance for regulatory requirements
The fixed-rate fee structure many providers offer helps businesses budget predictably while accessing expertise that would otherwise require multiple full-time specialists. This arrangement allows small businesses to focus on core operations while ensuring their IT infrastructure receives professional security management.
When evaluating managed security providers, consider their experience with businesses similar to yours, their response time commitments, and their approach to communication during incidents. The relationship should feel like a partnership rather than a vendor transaction, with the provider genuinely invested in your business success.
Businesses in Lethbridge and surrounding areas benefit from working with local managed service providers who understand regional business environments and can provide onsite support when situations demand in-person attention.
Cloud Security Considerations
Cloud computing offers tremendous advantages for small businesses, including scalability, accessibility, and reduced infrastructure costs. However, cloud adoption introduces specific security considerations for cyber security that organizations must address to maintain protection.
The shared responsibility model defines which security controls fall under cloud provider responsibilities versus customer obligations. Providers typically secure the underlying infrastructure, while customers remain responsible for properly configuring access controls, encrypting sensitive data, and managing user permissions.
Cloud Security Best Practices
- Enable multi-factor authentication for all cloud accounts
- Review and minimize user permissions regularly
- Encrypt sensitive data before uploading to cloud storage
- Monitor cloud access logs for unusual activity
- Implement strong password policies
- Configure automatic backup for cloud-hosted data
- Regularly review sharing settings and external access
Cloud misconfigurations represent one of the most common causes of data breaches. Organizations often inadvertently expose storage buckets, databases, or applications to public internet access, allowing attackers to access sensitive information without needing to bypass any security controls.
Regular security assessments of cloud configurations help identify and remediate exposures before attackers discover them. Many cloud platforms offer free security scanning tools that check for common misconfigurations, providing valuable insights for organizations without dedicated security teams.
Incident Response Planning
Despite best efforts, security incidents will occasionally occur, making comprehensive incident response planning essential for cyber security resilience. Organizations with documented response procedures minimize damage, restore operations faster, and maintain stakeholder confidence more effectively than those scrambling to improvise during crises.
An effective incident response plan includes:
- Clear roles and responsibilities for team members
- Communication protocols for internal and external stakeholders
- Step-by-step procedures for common incident types
- Contact information for key personnel and external resources
- Evidence preservation guidelines for potential legal action
- Recovery procedures and success criteria
- Post-incident review processes for continuous improvement
Testing response plans through tabletop exercises reveals gaps and ambiguities before real incidents occur. These exercises simulate various scenarios, allowing teams to practice coordination and decision-making in low-pressure environments. Quarterly tabletop exercises keep skills sharp and ensure new team members understand their roles.
Documentation should be accessible even during system outages, meaning critical response information should exist in both digital and physical formats. Contact lists, network diagrams, and basic procedures stored solely on potentially compromised systems provide little value during actual incidents.
Organizations should establish relationships with legal counsel, forensic investigators, and public relations professionals before incidents occur. Having these resources pre-identified and contractually arranged ensures faster response when every minute counts. For additional insights on protecting your business infrastructure, visit the Delphi Systems blog for regularly updated security guidance.
Integrating Security into Business Operations
The most effective approach for cyber security integrates protection seamlessly into daily business operations rather than treating it as a separate initiative. Security considerations should inform decisions about new software purchases, process changes, and business partnerships.
Before deploying new applications or services, evaluate their security implications. Consider questions like: What data will this system access? How does it authenticate users? Where is data stored? What happens if this system becomes compromised? These questions help identify potential risks before they materialize into actual incidents.
Vendor management processes should include security assessments for partners who access your systems or handle your data. Third-party relationships frequently provide attackers with indirect paths to target organizations, as demonstrated by numerous high-profile breaches that originated through compromised vendors.
Regular security reviews ensure that controls remain effective as your business evolves. Quarterly assessments should evaluate whether access permissions still align with current job responsibilities, whether network segmentation still reflects business requirements, and whether backup procedures still protect critical data adequately.
Building robust defenses requires ongoing attention, expertise, and resources that many small businesses struggle to maintain internally. Implementing the strategies outlined above creates multiple defensive layers that significantly enhance your organization's security posture against evolving threats. Delphi Systems Inc. helps small businesses in Lethbridge maintain secure, efficiently managed IT infrastructure through comprehensive managed services including cybersecurity, network monitoring, and data protection, all delivered through transparent fixed-rate pricing that lets you focus on growing your business with confidence.





