Small businesses face unprecedented challenges in protecting their digital assets. Every email, customer record, financial transaction, and proprietary document represents a potential vulnerability that cybercriminals actively exploit. The landscape of threats continues to evolve rapidly, with sophisticated attacks targeting organizations of all sizes. Understanding and implementing robust data and information security measures isn't just about technology-it's about protecting your business reputation, maintaining customer trust, and ensuring operational continuity in an increasingly connected world.
Understanding the Foundation of Data Protection
Data and information security encompasses far more than installing antivirus software or setting passwords. It represents a comprehensive approach to safeguarding digital assets throughout their entire lifecycle, from creation and storage to transmission and eventual deletion.
At its core, data-centric security focuses on protecting the information itself rather than just the perimeter defenses around it. This shift in perspective has become critical as businesses adopt cloud services, remote work arrangements, and mobile device usage. When data moves beyond traditional network boundaries, security must move with it.
The Critical Distinction Between Data and Information
Data refers to raw facts and figures-customer names, transaction amounts, timestamps. Information represents processed, organized data that provides meaningful context for decision-making. Both require protection, but the strategies differ based on sensitivity, usage patterns, and regulatory requirements.
Organizations must classify their assets into categories:
- Public information requiring minimal protection
- Internal data for employee access only
- Confidential material limited to specific roles
- Restricted data demanding highest security controls

Understanding these classifications enables businesses to allocate security resources efficiently. A manufacturing company's public product catalog doesn't require the same protection as customer credit card information or proprietary manufacturing processes.
Essential Security Practices Every Business Must Implement
The data security best practices outlined by Salesforce provide an excellent foundation, emphasizing authentication, encryption, and continuous monitoring. Small businesses in Lethbridge and surrounding areas particularly benefit from structured approaches that don't require extensive internal IT expertise.
Authentication and Access Control
Multi-factor authentication (MFA) has transitioned from optional to essential. Requiring users to verify identity through multiple methods-something they know (password), something they have (phone), or something they are (fingerprint)-dramatically reduces unauthorized access risks.
| Authentication Method | Security Level | User Convenience | Implementation Cost |
|---|---|---|---|
| Password Only | Low | High | Minimal |
| MFA (2-Factor) | High | Medium | Low |
| MFA (3-Factor) | Very High | Lower | Moderate |
| Biometric | Very High | High | Higher |
Access control extends beyond initial login. Role-based access control (RBAC) ensures employees access only information necessary for their responsibilities. An accounting team member doesn't need access to HR personnel files, and marketing staff shouldn't view financial ledgers.
Encryption as Standard Practice
Data encryption transforms readable information into coded format accessible only with proper decryption keys. Modern data and information security strategies implement encryption at multiple levels:
- Data at rest: Files stored on servers, computers, and backup systems
- Data in transit: Information moving across networks, internet connections, or cloud services
- Data in use: Active files being processed or edited
Small businesses often overlook encryption for internal communications and file sharing. However, even local network traffic can be intercepted. Implementing encryption doesn't require technical expertise when working with experienced managed IT service providers.
Building a Security-Conscious Organizational Culture
Technology alone cannot protect businesses from security breaches. According to Harvard’s information security best practices, human factors-particularly phishing susceptibility-remain primary attack vectors.
Employee Training and Awareness
Regular security awareness training transforms employees from vulnerabilities into defensive assets. Effective programs cover:
- Recognizing phishing emails and suspicious communications
- Proper password creation and management techniques
- Safe browsing habits and download protocols
- Mobile device security for remote work
- Incident reporting procedures
Training shouldn't be annual checkbox exercises. Quarterly sessions with real-world examples and simulated phishing tests maintain awareness and reinforce behaviors.

Creating Accountability Through Policy
Written security policies establish clear expectations and consequences. Comprehensive policies address:
Acceptable use: Defining appropriate technology usage for business purposes
Password requirements: Complexity standards and change frequencies
Device management: Personal device usage and company equipment handling
Data handling: Classification procedures and sharing protocols
Incident response: Steps for reporting suspected breaches
Policies remain meaningless without enforcement. Regular audits and compliance checks demonstrate organizational commitment to data and information security.
Technical Infrastructure for Robust Protection
Small businesses require enterprise-level protection without enterprise-level complexity. Strategic technology investments create multiple defensive layers that work synergistically.
Network Security Fundamentals
Firewalls serve as first-line defense, filtering incoming and outgoing traffic based on predetermined security rules. Modern next-generation firewalls (NGFW) incorporate:
- Deep packet inspection analyzing data contents
- Intrusion prevention systems blocking suspicious activities
- Application awareness controlling specific program access
- Threat intelligence integration from global databases
Network segmentation divides infrastructure into isolated zones. Guest WiFi networks operate separately from business systems. Financial data resides on different network segments than general file storage. Breaches in one area don't automatically compromise everything.
Continuous Monitoring and Threat Detection
Passive security measures are insufficient against sophisticated threats. Security Information and Event Management (SIEM) systems aggregate data from multiple sources, analyzing patterns that indicate potential breaches.
Real-time monitoring identifies:
- Unusual login attempts or access patterns
- Large data transfers to unknown destinations
- Malware signatures and suspicious file behaviors
- System configuration changes without authorization
- Failed authentication attempts exceeding thresholds
For small businesses, outsourcing monitoring to Delphi Systems Inc. provides 24/7 vigilance without maintaining internal security operations centers.
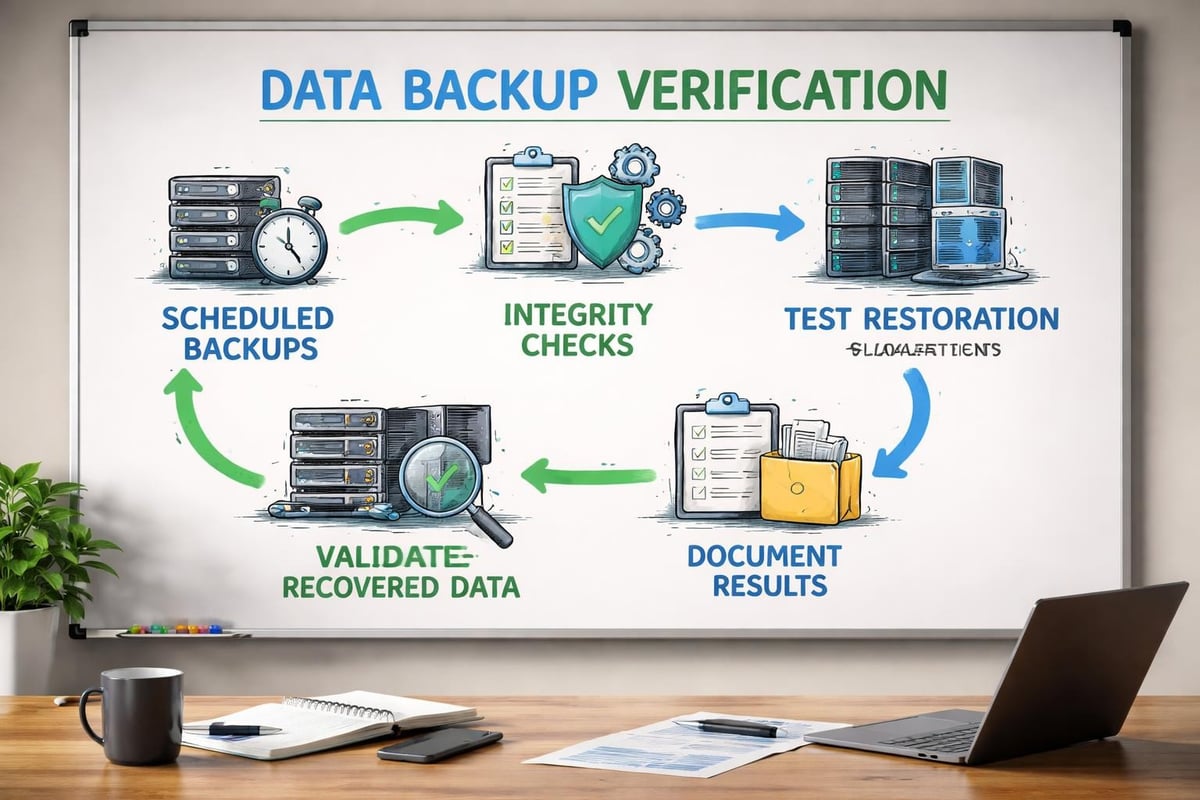
Data Backup and Recovery Strategies
Data and information security isn't solely about preventing breaches-it's ensuring business continuity when incidents occur. Comprehensive backup strategies follow the 3-2-1 rule:
- 3 copies of data exist (original plus two backups)
- 2 different media types store backups
- 1 copy resides off-site or in cloud storage
Backup Frequency and Testing
| Data Type | Backup Frequency | Retention Period | Recovery Priority |
|---|---|---|---|
| Financial Records | Daily | 7 years | Critical |
| Customer Database | Hourly | 3 years | Critical |
| Email Systems | Daily | 1 year | High |
| Project Files | Daily | 2 years | Medium |
| General Documents | Weekly | 1 year | Low |
Regular restoration testing validates backup integrity. Discovering corrupted backups during actual emergencies compounds disasters. Monthly test recoveries ensure systems function properly and staff understand procedures.
Compliance and Regulatory Considerations
Various regulations mandate specific data and information security measures. While requirements vary by industry and location, fundamental principles remain consistent.
Common Regulatory Frameworks
PIPEDA (Personal Information Protection and Electronic Documents Act) governs how Canadian businesses collect, use, and disclose personal information. Compliance requires:
- Obtaining consent for data collection and usage
- Limiting collection to necessary information only
- Protecting information with appropriate safeguards
- Providing individuals access to their data
- Maintaining accuracy of personal information
Industry-specific regulations add layers. Healthcare organizations must address patient privacy under provincial health information acts. Financial institutions face additional requirements for transaction security and fraud prevention.
Documentation and Audit Trails
Compliance demands documented evidence of security practices. Comprehensive audit trails record:
- Who accessed specific data and when
- What changes occurred to sensitive information
- System configuration modifications
- Security incident responses and resolutions
- Policy reviews and employee training completion
Digital recordkeeping systems automate much of this documentation burden, but GeeksforGeeks data security best practices emphasize regular review processes to identify gaps and improvement opportunities.
Cloud Security Considerations
Cloud adoption transforms data and information security challenges. Shared responsibility models mean cloud providers secure infrastructure while businesses protect data and access management.
Securing Cloud Environments
Identity and access management (IAM) becomes paramount in cloud contexts. Strong IAM practices include:
- Implementing single sign-on (SSO) for centralized authentication
- Regularly reviewing and revoking unnecessary permissions
- Enforcing MFA for administrative accounts
- Monitoring privileged account activities
- Automating user provisioning and de-provisioning
Data encryption in cloud environments should use customer-managed encryption keys rather than provider-managed keys. This ensures only your organization can decrypt data, even if cloud infrastructure is compromised.
Vendor Security Assessment
Not all cloud providers maintain equivalent security standards. Thorough vendor evaluations examine:
- Certifications: SOC 2, ISO 27001, and industry-specific compliance
- Data location: Physical server locations and data sovereignty
- Incident response: Breach notification procedures and timelines
- Service level agreements: Uptime guarantees and security commitments
- Exit strategies: Data portability and deletion verification
The American Express guide to data security emphasizes conducting thorough vendor due diligence before entrusting sensitive business information to third parties.
Mobile Device and Remote Work Security
Remote work expansion has dissolved traditional network perimeters. Employees accessing business systems from home offices, coffee shops, and client sites require comprehensive mobile security strategies.
Mobile Device Management
Mobile Device Management (MDM) solutions enforce security policies across smartphones, tablets, and laptops. Core capabilities include:
- Remote device wiping if lost or stolen
- Application whitelisting and blacklisting
- Encryption requirement enforcement
- Operating system update management
- Containerization separating business and personal data
Bring Your Own Device (BYOD) policies require careful balancing of security needs against employee privacy concerns. Clear policies define acceptable personal device usage and security requirements.
Virtual Private Networks
VPNs create encrypted tunnels between remote devices and business networks. All internet traffic routes through company infrastructure, protecting data from interception on public WiFi networks.
However, VPNs alone are insufficient. Endpoint security solutions on individual devices provide additional protection:
- Real-time malware scanning and removal
- Host-based firewalls controlling network connections
- Application control preventing unauthorized software installation
- Data loss prevention monitoring sensitive information movement
Incident Response Planning
Despite best preventive measures, security incidents eventually occur. Structured incident response plans minimize damage and accelerate recovery.
Response Team Structure
Designate specific roles and responsibilities:
Incident Commander: Coordinates overall response and makes critical decisions
Technical Lead: Investigates technical aspects and implements containment
Communications Lead: Manages internal and external communications
Legal Advisor: Addresses regulatory and legal implications
Business Continuity Lead: Ensures critical operations continue
Small businesses often lack resources for dedicated response teams. Partnering with managed IT service providers ensures expert assistance during critical incidents.
Response Phases
Effective incident response follows structured phases:
- Detection and Analysis: Identify and assess the incident scope
- Containment: Isolate affected systems to prevent spread
- Eradication: Remove threat causes from environment
- Recovery: Restore systems and verify normal operations
- Post-Incident Review: Document lessons learned and improve processes
Each phase requires specific actions and decision criteria. Regular tabletop exercises test response procedures and identify gaps before real incidents occur.
Measuring Security Effectiveness
Data and information security requires ongoing assessment and improvement. Key performance indicators (KPIs) provide objective measurements of security posture.
Essential Security Metrics
| Metric | Description | Target Range |
|---|---|---|
| Mean Time to Detect (MTTD) | Average time identifying security incidents | Under 24 hours |
| Mean Time to Respond (MTTR) | Average time containing and resolving incidents | Under 4 hours |
| Patch Compliance Rate | Percentage of systems with current security updates | Above 95% |
| Phishing Test Click Rate | Employees clicking simulated phishing emails | Below 5% |
| Security Audit Score | Compliance with internal security policies | Above 90% |
Regular vulnerability assessments identify weaknesses before attackers exploit them. Penetration testing simulates real attacks to validate defensive measures.
Continuous Improvement Culture
Security isn't a destination but an ongoing journey. Quarterly security reviews examine:
- Recent incidents and near-misses
- New threat intelligence and attack vectors
- Technology updates and capability enhancements
- Policy effectiveness and enforcement gaps
- Training program results and employee feedback
Documented improvement plans track progress against identified weaknesses. Executive sponsorship ensures adequate resources for critical security initiatives.
Balancing Security with Business Operations
Excessive security measures can hinder productivity and frustrate employees. Optimal data and information security balances protection against usability.
User Experience Considerations
Security implementations should minimize friction for legitimate users while blocking unauthorized access. Examples include:
- Single sign-on reducing password fatigue
- Adaptive authentication adjusting requirements based on risk levels
- Automated compliance tools reducing manual processes
- Self-service password resets decreasing support tickets
Regular user feedback identifies security measures causing productivity issues. Adjustments maintain protection while improving workflows.
Cost-Benefit Analysis
Security investments compete with other business priorities. Rational decision-making requires understanding:
Risk probability: Likelihood of specific threats materializing
Impact severity: Potential damage from successful attacks
Control effectiveness: How well measures reduce risk
Implementation costs: Total expenses including ongoing maintenance
Quantifying risks in financial terms enables comparison with security investment costs. A $50,000 security solution preventing potential $500,000 breaches represents sound investment.
Protecting business data requires comprehensive strategies combining technology, processes, and people. From encryption and access controls to employee training and incident response planning, each element contributes to overall security posture. Small businesses in Lethbridge don't need to navigate these complexities alone. Delphi Systems Inc. provides expert managed IT services that implement robust data and information security measures tailored to your specific needs, allowing you to focus on growing your business while maintaining confidence that your digital assets remain protected.