Small businesses face an increasingly complex threat landscape in 2026, where cybersecurity information security has become a critical business function rather than an optional investment. The convergence of cybersecurity practices and information security principles creates a comprehensive approach to protecting digital assets, sensitive data, and operational continuity. For businesses in Lethbridge and across Alberta, understanding how these disciplines work together is essential for maintaining competitive advantage and customer trust. This article explores the fundamental components, practical implementation strategies, and measurable outcomes that small businesses should prioritize when building their security posture.
Understanding the Cybersecurity Information Security Framework
The relationship between cybersecurity and information security represents two complementary disciplines that work in tandem to protect organizational assets. Cybersecurity focuses on defending computers, networks, and systems from digital attacks, while information security encompasses the broader protection of data in all forms, including physical and digital. When combined, cybersecurity information security creates a holistic defense strategy.
The NIST Cybersecurity Framework provides an industry-standard approach that small businesses can adopt to structure their security programs. This framework organizes security activities into five core functions:
- Identify: Understanding business context, resources, and risks
- Protect: Implementing safeguards for critical infrastructure
- Detect: Developing capabilities to identify security events
- Respond: Taking action when incidents occur
- Recover: Restoring capabilities after security events
Small businesses benefit from this structured approach because it provides clear guidance without requiring extensive security expertise. The framework scales to fit organizational size and complexity, making it practical for companies with limited IT resources.
Building a Risk-Based Security Program
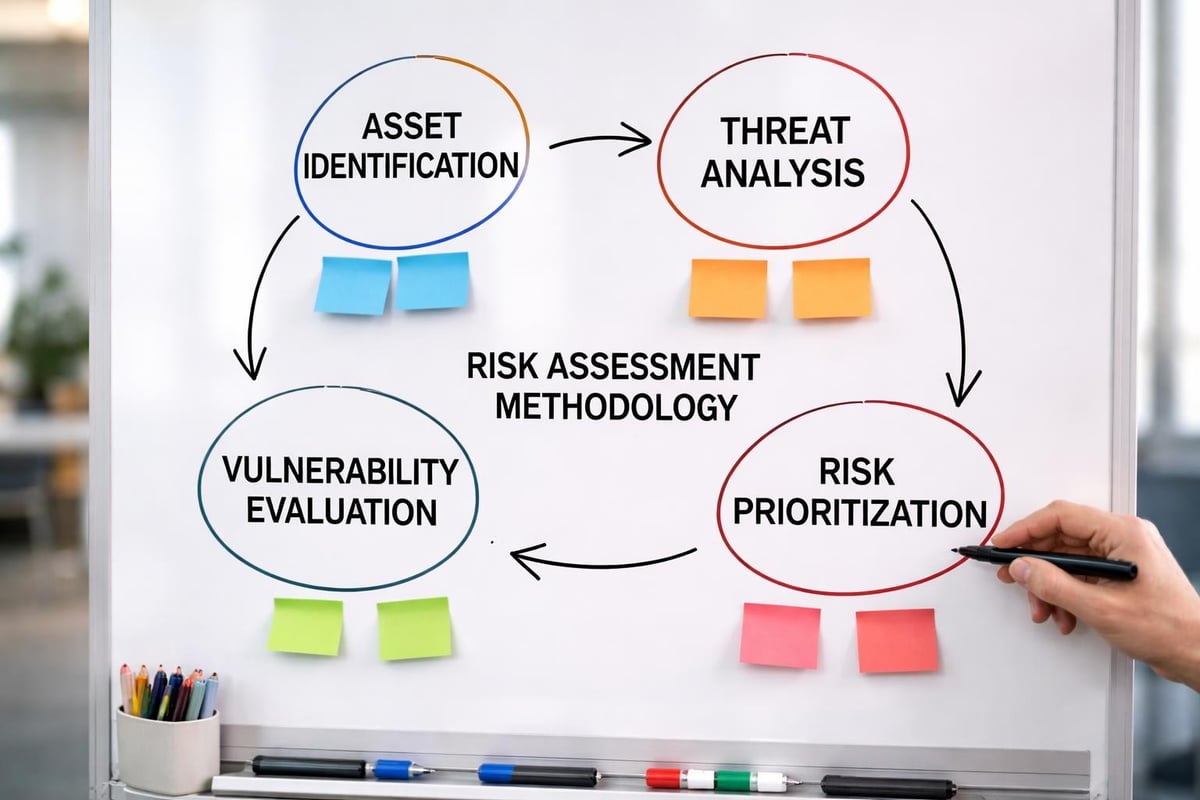
Effective cybersecurity information security begins with understanding what needs protection and why. Risk assessment forms the foundation of any security program, helping businesses allocate limited resources to areas of greatest concern.
Key risk assessment steps include:
- Cataloging all information assets (customer data, financial records, intellectual property)
- Identifying potential threats (ransomware, phishing, insider threats, system failures)
- Evaluating existing controls and their effectiveness
- Calculating likelihood and impact of various scenarios
- Prioritizing remediation efforts based on risk levels
This process reveals where vulnerabilities exist and which security investments deliver the highest return. For example, a professional services firm might discover that client data stored in cloud applications represents the highest risk, prompting investment in enhanced access controls and encryption.
Essential Security Controls for Small Businesses
Implementing practical security controls transforms abstract cybersecurity information security concepts into tangible protection. The controls selected should align with identified risks and available resources, creating layers of defense that work together.
Access Management and Authentication
Controlling who can access systems and data represents one of the most effective security measures. Multi-factor authentication (MFA) adds critical protection beyond passwords alone, requiring users to verify their identity through multiple methods.
Organizations should implement:
- Role-based access control (RBAC) that grants permissions based on job functions
- Privileged access management for administrative accounts with elevated permissions
- Regular access reviews to remove permissions no longer needed
- Strong password policies enforced through technical controls
These measures significantly reduce the risk of unauthorized access, even when credentials are compromised through phishing or other attacks.
Network Security Architecture
Network segmentation and monitoring create visibility into traffic patterns and contain potential breaches. Small businesses can implement effective network security without enterprise-scale complexity.
| Security Layer | Purpose | Implementation Example |
|---|---|---|
| Firewall | Block unauthorized traffic | Next-generation firewall with application awareness |
| IDS/IPS | Detect and prevent attacks | Network-based intrusion prevention system |
| VPN | Secure remote access | Site-to-site and client VPN connections |
| Network Monitoring | Identify anomalies | Continuous traffic analysis and alerting |
| Segmentation | Limit breach scope | Separate networks for guest, internal, and critical systems |
This layered approach ensures that even if attackers breach one security control, additional defenses prevent complete compromise.
Data Protection and Privacy Compliance
Cybersecurity information security extends beyond preventing unauthorized access to include proper handling, storage, and disposal of sensitive information. The ISO/IEC 27001 information security management standard provides a comprehensive framework for protecting information throughout its lifecycle.
Encryption and Data Loss Prevention
Encryption transforms readable data into an unreadable format without the proper decryption key, protecting information both in transit and at rest. Small businesses should encrypt:
- Data stored on laptops, mobile devices, and removable media
- Information transmitted over networks, including email
- Database contents containing sensitive customer or financial data
- Cloud storage and backup repositories
Data loss prevention (DLP) technologies monitor and control data movement, preventing accidental or intentional leakage. These systems can block attempts to email confidential documents to personal accounts or copy sensitive files to USB drives.
Backup and Disaster Recovery
Regular, tested backups form a critical component of cybersecurity information security strategy. The 3-2-1 backup rule provides a reliable framework:
- Maintain three copies of important data
- Store backups on two different media types
- Keep one copy offsite or in the cloud
Backup strategies must address both operational recovery and ransomware scenarios. Immutable backups that cannot be encrypted or deleted by attackers ensure recovery options remain available even during an active attack.

Threat Detection and Incident Response
Even with strong preventive controls, organizations must assume that breaches will occur and prepare accordingly. Cybersecurity information security programs require capabilities to detect, analyze, and respond to security incidents quickly.
Security Monitoring and Analysis
Security Information and Event Management (SIEM) systems collect and analyze log data from across the IT environment, identifying patterns that indicate potential security incidents. For small businesses, managed security services provide access to these capabilities without significant capital investment.
Effective monitoring focuses on:
- Failed authentication attempts suggesting password attacks
- Unusual data access patterns indicating compromised accounts
- Network traffic to known malicious destinations
- Changes to critical system configurations
- Privilege escalation activities
The Cybersecurity and Infrastructure Security Agency publishes regular alerts about emerging threats and recommended mitigations that organizations can incorporate into their monitoring strategies.
Incident Response Planning
Having a documented incident response plan ensures coordinated, effective action when security events occur. The plan should define:
- Roles and responsibilities for incident response team members
- Communication protocols for internal and external stakeholders
- Escalation procedures based on incident severity
- Containment strategies to limit damage
- Recovery steps to restore normal operations
- Post-incident review processes to improve future responses
Small businesses should conduct tabletop exercises annually to test these plans and identify gaps before real incidents occur.
Security Awareness and Human Factors
Technology controls alone cannot achieve comprehensive cybersecurity information security. Human behavior remains both the greatest vulnerability and most important defense layer.
Employee Training Programs
Regular security awareness training helps employees recognize and respond appropriately to threats. Effective programs address:
- Phishing recognition: Identifying suspicious emails and websites
- Password hygiene: Creating and managing strong credentials
- Data handling: Properly classifying and protecting sensitive information
- Physical security: Securing devices and work areas
- Incident reporting: Knowing when and how to report potential security issues
Training should occur during onboarding and at least quarterly thereafter, with topics rotating to address emerging threats. Simulated phishing campaigns test knowledge retention and identify employees who need additional support.
Creating a Security-Conscious Culture
Beyond formal training, organizations benefit from fostering a culture where security becomes everyone's responsibility. Leadership commitment demonstrates that cybersecurity information security represents a business priority rather than an IT concern alone.
Culture-building strategies include:
- Executive participation in security initiatives
- Recognition for employees who identify and report threats
- Clear policies that balance security with productivity
- Open communication about security incidents and lessons learned
- Regular reminders about current threat campaigns
Compliance and Regulatory Considerations
Many industries face specific cybersecurity information security requirements through regulations and contractual obligations. Understanding applicable requirements helps businesses avoid penalties and maintain customer trust.
Common Compliance Frameworks
Different sectors and business relationships impose various security standards:
| Framework | Applicability | Key Requirements |
|---|---|---|
| PCI DSS | Payment card processing | Encryption, access controls, network segmentation |
| PIPEDA | Canadian personal information | Consent, safeguards, accountability |
| SOC 2 | Service providers | Security, availability, confidentiality controls |
| HIPAA | Healthcare information (US) | Privacy, security, breach notification |
| GDPR | EU personal data | Data protection, privacy rights |
Organizations should identify which frameworks apply to their operations and implement controls that satisfy multiple requirements simultaneously.
Documentation and Audit Preparation
Maintaining evidence of cybersecurity information security practices proves essential for compliance validation. Documentation should include:
- Security policies and procedures
- Risk assessment results and remediation plans
- System inventories and data flow diagrams
- Control testing evidence and results
- Incident logs and response documentation
- Training records and acknowledgments
Regular internal audits help identify gaps before external assessors review controls, reducing the risk of compliance failures.

Emerging Threats and Future Considerations
The cybersecurity information security landscape continues to evolve as attackers develop new techniques and technologies create fresh vulnerabilities. Small businesses must stay informed about emerging risks to maintain effective protection.
Current Threat Trends in 2026
Recent threat intelligence from CISA and other sources highlights several areas of concern:
- AI-powered attacks that adapt to defensive measures in real-time
- Supply chain compromises targeting software vendors and service providers
- Ransomware-as-a-service lowering barriers for criminal operations
- Cloud misconfigurations exposing sensitive data through improper settings
- IoT vulnerabilities creating entry points through connected devices
Addressing these threats requires both technical controls and strategic awareness. For instance, vendor security assessments become critical when evaluating new software or service providers.
Adapting Security Programs Over Time
Cybersecurity information security represents an ongoing process rather than a one-time project. Organizations should review and update their security programs at least annually, or whenever significant changes occur:
- New business initiatives or service offerings
- Technology infrastructure updates
- Regulatory requirement changes
- Significant security incidents (internal or industry-wide)
- Merger or acquisition activities
This continuous improvement approach ensures that security capabilities mature alongside the business and threat environment.
Practical Implementation for Small Businesses
Translating cybersecurity information security concepts into action requires practical, budget-conscious approaches that fit small business realities. Many effective security measures require more process discipline than financial investment.
Building Security Without Breaking the Budget
Quick-win security improvements include:
- Enabling MFA on all critical systems and applications
- Implementing automated patch management for operating systems and applications
- Configuring endpoint protection with next-generation antivirus capabilities
- Establishing regular backup schedules with tested recovery procedures
- Deploying web filtering to block access to malicious sites
These foundational controls address the majority of common attack vectors and demonstrate security commitment to customers and partners.
Leveraging Managed Services
Small businesses often lack the resources to employ dedicated security specialists. Delphi Systems Inc. and similar managed service providers offer access to enterprise-grade security capabilities through fixed-fee arrangements that make costs predictable.
Managed security services typically include:
- Continuous network and system monitoring
- Patch and vulnerability management
- Security incident response
- Compliance reporting and documentation
- Strategic security planning and roadmap development
This partnership model allows businesses to focus on core operations while ensuring their cybersecurity information security needs receive expert attention.
Measuring Security Effectiveness
Establishing metrics helps demonstrate the value of cybersecurity information security investments and identify areas needing improvement. Useful measurements include:
| Metric Category | Example Measurements | Business Value |
|---|---|---|
| Preventive Controls | Percentage of systems with current patches | Reduces vulnerability exposure |
| Detective Controls | Mean time to detect security incidents | Limits breach duration and damage |
| Response Capabilities | Mean time to contain and recover | Minimizes operational disruption |
| User Awareness | Phishing simulation click rates | Reduces human-factor risks |
| Compliance Posture | Control test pass rates | Avoids penalties and maintains trust |
Regular reporting of these metrics to leadership maintains awareness and supports continued investment in security capabilities.
Integration with Business Operations
Effective cybersecurity information security integrates seamlessly with business processes rather than creating obstacles to productivity. This balance requires understanding operational needs while maintaining appropriate risk management.
Secure by Design Principles
Incorporating security considerations during planning phases prevents costly retrofitting later. When evaluating new systems, applications, or business processes, assess:
- Data sensitivity and required protection levels
- User access patterns and authentication requirements
- Integration points with existing systems
- Regulatory or contractual security obligations
- Incident response and recovery capabilities
This proactive approach embeds security into the foundation rather than adding it as an afterthought.
Vendor and Third-Party Risk Management
Extended business ecosystems introduce security dependencies on external organizations. Cybersecurity information security programs must address these relationships through:
- Security questionnaires and assessments for new vendors
- Contract provisions requiring specific security controls
- Regular reviews of vendor security posture
- Incident notification requirements
- Right-to-audit clauses for critical suppliers
These practices extend security boundaries beyond directly controlled systems to encompass the entire operational ecosystem.
Implementing comprehensive cybersecurity information security requires commitment, planning, and ongoing attention, but the investment protects business continuity, customer trust, and competitive position in an increasingly digital economy. Small businesses in Lethbridge and surrounding areas can achieve robust security without overwhelming complexity by following proven frameworks, prioritizing risk-based controls, and leveraging expert guidance. Delphi Systems Inc. specializes in helping small businesses build and maintain effective security programs through managed IT services that combine technical expertise with fixed-rate pricing, allowing you to focus on growing your business while ensuring your IT infrastructure remains secure and efficiently managed.





