Network security threats continue to evolve at an alarming pace, making it increasingly difficult for small businesses to protect their digital assets. A cyber intrusion detection system serves as a critical defense mechanism that monitors network activity, identifies suspicious behavior, and alerts IT teams to potential security breaches before they cause significant damage. For businesses in Lethbridge and surrounding areas, understanding how these systems work and implementing them effectively can mean the difference between maintaining operational continuity and suffering costly downtime from cyberattacks. This comprehensive guide explores the fundamental components, deployment strategies, and practical considerations that small business owners need to know when evaluating intrusion detection solutions for their IT infrastructure.
Understanding Cyber Intrusion Detection Systems
A cyber intrusion detection system (IDS) functions as a vigilant security monitor that continuously analyzes network traffic and system activities for signs of malicious behavior or policy violations. These sophisticated tools examine data packets, log files, and system calls to detect patterns that indicate potential security threats.
The technology operates through two primary detection methodologies: signature-based detection and anomaly-based detection. Signature-based systems compare network traffic against a database of known attack patterns, similar to how antivirus software identifies malware. Anomaly-based systems establish a baseline of normal network behavior and flag activities that deviate significantly from established patterns.
Network-Based vs. Host-Based Detection
Organizations can deploy intrusion detection capabilities at multiple levels within their IT infrastructure. Network-based intrusion detection systems (NIDS) monitor traffic across entire network segments, analyzing packets as they traverse routers and switches. These systems excel at identifying network-layer attacks, port scans, and distributed denial-of-service attempts.
Host-based intrusion detection systems (HIDS) operate on individual servers or workstations, monitoring system logs, file integrity, and application behavior. According to research on host-based intrusion detection, these systems provide granular visibility into endpoint activities that network-based solutions might miss.

Key differences between deployment types:
- Network-Based IDS: Monitors multiple devices simultaneously, requires specialized network placement, analyzes encrypted traffic limitations
- Host-Based IDS: Provides detailed endpoint visibility, consumes system resources, requires installation on each protected device
- Hybrid Approach: Combines both methodologies for comprehensive coverage across network and endpoint layers
Components of an Effective Cyber Intrusion Detection System
Building a robust intrusion detection capability requires multiple integrated components working together seamlessly. The architecture typically includes sensors, analysis engines, management consoles, and alert mechanisms that form a cohesive security monitoring ecosystem.
Sensors represent the data collection layer, positioned strategically throughout the network infrastructure to capture relevant traffic and system events. These sensors feed information to analysis engines that apply detection algorithms and correlation rules to identify potential security incidents.
Detection Engines and Analysis Methods
Modern cyber intrusion detection systems leverage multiple analysis techniques to improve accuracy and reduce false positives. Statistical analysis compares current network behavior against historical baselines to identify anomalies. Protocol analysis verifies that network communications adhere to expected standards and identifies protocol-based attacks.
The NIST guide on intrusion detection and prevention systems emphasizes the importance of selecting appropriate detection methodologies based on organizational requirements and threat landscapes.
| Analysis Method | Strengths | Limitations | Best Use Cases |
|---|---|---|---|
| Signature-Based | High accuracy for known threats, Low false positives | Cannot detect zero-day attacks | Detecting established malware, Known exploit attempts |
| Anomaly-Based | Identifies unknown threats, Adapts to new patterns | Higher false positive rates | Zero-day detection, Insider threat monitoring |
| Protocol Analysis | Detects protocol violations, Standards enforcement | Resource intensive | Web application protection, Email security |
Alert Management and Response Integration
Detection without effective response delivers limited security value. A comprehensive cyber intrusion detection system incorporates alert prioritization, automated response capabilities, and integration with broader security orchestration platforms.
Alert fatigue represents a significant challenge for security teams overwhelmed by high volumes of notifications. Modern systems employ machine learning algorithms to correlate related events, suppress duplicate alerts, and prioritize incidents based on severity and business impact.
Deployment Strategies for Small Business Networks
Small businesses face unique challenges when implementing intrusion detection capabilities. Limited IT budgets, smaller technical teams, and resource constraints require pragmatic approaches that balance security effectiveness with operational feasibility.
The deployment process begins with a comprehensive network assessment to identify critical assets, data flows, and potential vulnerability points. This assessment informs sensor placement decisions and helps prioritize monitoring efforts on high-value targets.
Selecting Appropriate Detection Technologies
Choosing the right cyber intrusion detection system requires evaluating multiple factors including network architecture, compliance requirements, available expertise, and budget constraints. Open-source solutions like Snort provide powerful capabilities without licensing costs, though they require technical expertise for configuration and maintenance.
Evaluation criteria for small businesses:
- Deployment complexity: Consider ease of installation, configuration requirements, and ongoing maintenance demands
- Scalability: Ensure the solution can grow with business expansion and increasing network complexity
- Integration capabilities: Verify compatibility with existing security tools, firewalls, and SIEM platforms
- Support availability: Assess vendor support options, community resources, and documentation quality
- Total cost of ownership: Calculate licensing, hardware, personnel, and training expenses over multi-year periods

Managed Detection Services
For small businesses lacking dedicated security personnel, managed detection and response services offer an attractive alternative to in-house deployment. These services provide expert monitoring, 24/7 threat analysis, and incident response capabilities without requiring internal expertise.
Managed service providers operate security operations centers staffed with analysts who monitor client networks continuously. When a cyber intrusion detection system identifies suspicious activity, trained professionals investigate alerts, filter false positives, and coordinate response actions.
Integration with Broader Security Frameworks
Intrusion detection systems deliver maximum value when integrated into comprehensive security architectures rather than operating as isolated solutions. This integration enables correlation of security events across multiple data sources, providing context that improves detection accuracy and response effectiveness.
Security information and event management (SIEM) platforms aggregate logs and alerts from diverse security tools including firewalls, antivirus systems, and intrusion detection sensors. This centralized visibility enables security teams to identify complex attack patterns that might appear innocuous when viewed in isolation.
Threat Intelligence Sharing
Modern cyber intrusion detection systems benefit from threat intelligence feeds that provide real-time information about emerging threats, malicious IP addresses, and attack indicators. Research on collaborative threat intelligence sharing demonstrates how organizations can collectively improve detection capabilities while preserving data privacy.
Threat intelligence integration enhances signature databases, informs anomaly detection baselines, and enables proactive blocking of known malicious actors. Industry-specific intelligence sharing groups provide particularly valuable insights tailored to sector-specific threats.
| Integration Type | Security Benefits | Implementation Considerations |
|---|---|---|
| SIEM Platform | Centralized visibility, Advanced correlation | Significant configuration effort, Resource requirements |
| Threat Intelligence | Current attack indicators, Proactive defense | Feed quality varies, Requires validation |
| Firewall Systems | Automated blocking, Unified policy | Coordination complexity, Testing requirements |
| Endpoint Protection | Cross-layer detection, Complete visibility | Agent management, Performance impact |
Tuning and Optimization for Maximum Effectiveness
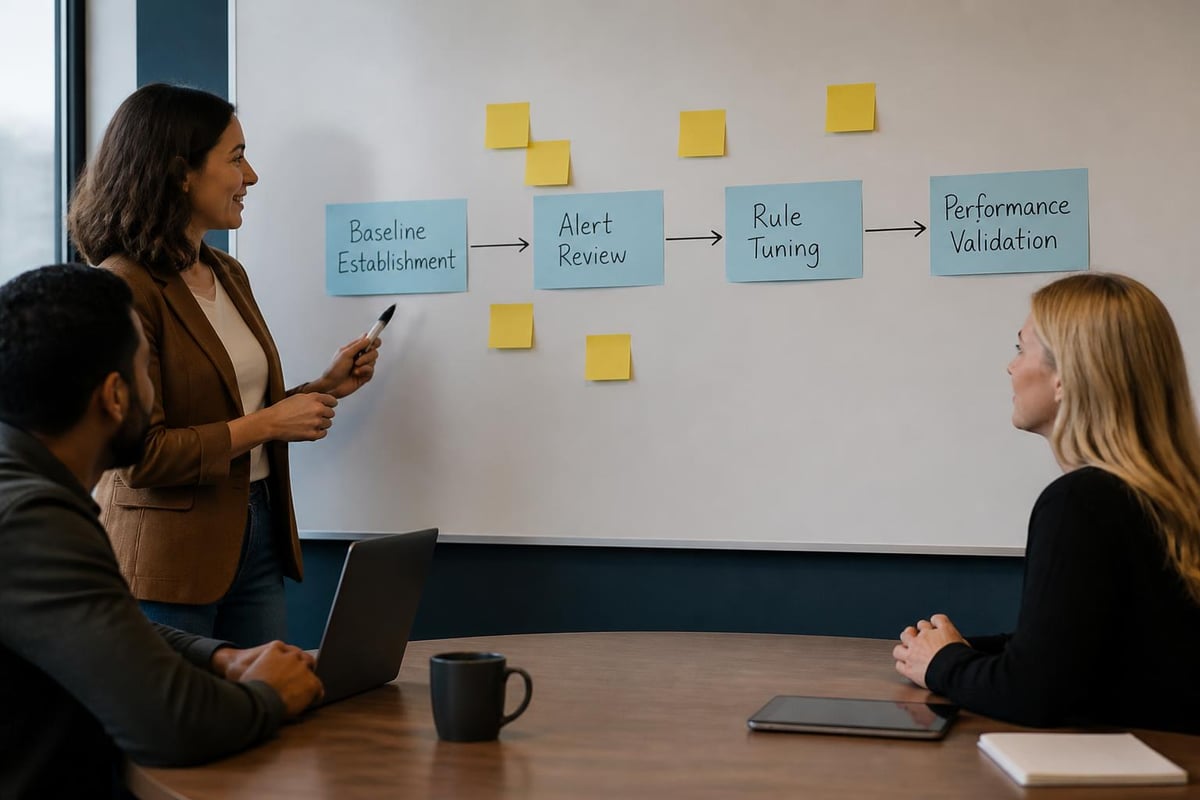
Deploying a cyber intrusion detection system represents just the beginning of an ongoing optimization process. Initial deployments typically generate high volumes of false positives that require careful tuning to achieve acceptable signal-to-noise ratios.
Baseline establishment consumes the first several weeks after deployment, during which the system learns normal network behavior patterns. Security teams must review alerts regularly, classify true positives versus false positives, and adjust detection rules accordingly.
Rule Customization and Policy Development
Generic detection rules provide basic security coverage but rarely address organization-specific requirements effectively. Customizing detection policies to reflect business processes, application behaviors, and acceptable use policies significantly improves detection accuracy.
Optimization best practices:
- Document all rule modifications with justification and expected outcomes
- Test rule changes in monitoring mode before enabling enforcement actions
- Review detection performance metrics weekly during initial deployment phases
- Establish alert escalation procedures based on severity classifications
- Schedule quarterly reviews of detection effectiveness and coverage gaps
Performance Monitoring and Capacity Planning
A cyber intrusion detection system must maintain adequate performance levels to analyze network traffic without introducing latency or dropping packets. According to Department of Homeland Security guidance, monitoring system health metrics ensures detection capabilities remain effective as network traffic volumes increase.
Regular capacity assessments identify when sensor upgrades or architectural changes become necessary to maintain complete visibility. Packet capture rates, analysis throughput, and storage utilization metrics provide early warning of capacity constraints.
Advanced Detection Capabilities and Emerging Technologies
The cyber threat landscape continues evolving rapidly, driving innovation in intrusion detection technologies. Machine learning and artificial intelligence applications improve detection accuracy while reducing manual analysis requirements.
Deep learning techniques show particular promise for identifying subtle attack patterns that evade traditional detection methods. Research on convolutional neural networks for intrusion detection demonstrates significant improvements in detecting sophisticated attacks against cyber-physical systems.
Behavioral Analytics and User Monitoring
Modern cyber intrusion detection systems increasingly incorporate user and entity behavior analytics (UEBA) to identify insider threats and compromised credentials. These capabilities establish individual user behavior baselines and flag activities that deviate from established patterns.
UEBA technologies detect lateral movement within networks, privilege escalation attempts, and unusual data access patterns that indicate account compromise. This behavioral approach complements traditional network-based detection methodologies.
Behavioral detection capabilities:
- Abnormal login times and locations for user accounts
- Unusual application access patterns or data queries
- Privilege escalation attempts and administrative tool usage
- Atypical network connections and data transfer volumes
- Deviation from established workflow patterns
Addressing Data Quality Challenges
Detection accuracy depends heavily on the quality and completeness of input data. Standardized feature sets for intrusion detection datasets help address inconsistencies that reduce detection effectiveness and complicate system comparisons.
Organizations must ensure comprehensive logging across all network devices, applications, and endpoints. Missing data creates blind spots that attackers can exploit to avoid detection during reconnaissance and attack execution phases.
Compliance and Regulatory Considerations
Many industries mandate specific intrusion detection capabilities as part of regulatory compliance frameworks. Healthcare organizations subject to HIPAA requirements, financial institutions governed by PCI-DSS standards, and government contractors bound by NIST standards must implement appropriate detection controls.
A properly configured cyber intrusion detection system provides valuable audit evidence demonstrating security monitoring capabilities and incident response readiness. Compliance auditors frequently review detection policies, alert response procedures, and investigation documentation during assessments.
Documentation and Audit Trail Requirements
Regulatory frameworks typically require organizations to maintain detailed records of security events, investigation activities, and response actions. Intrusion detection systems must capture sufficient detail to support forensic analysis while retaining logs for mandated periods.
| Regulation | IDS Requirements | Retention Period | Key Focus Areas |
|---|---|---|---|
| HIPAA | Security monitoring, Access controls | 6 years | Protected health information access |
| PCI-DSS | Network monitoring, Alert response | 1 year minimum | Cardholder data environment |
| NIST 800-53 | Continuous monitoring, Incident detection | Organization-defined | Federal information systems |
| GDPR | Security measures, Breach detection | Varies by member state | Personal data protection |
Implementation Roadmap for Small Businesses
Successful cyber intrusion detection system deployment follows a structured implementation approach that minimizes disruption while establishing effective security monitoring capabilities. The roadmap typically spans three to six months depending on network complexity and organizational readiness.
Phase one focuses on planning and assessment activities including network documentation, asset inventory, and requirements definition. This foundation ensures subsequent deployment phases address actual business needs rather than generic security recommendations.
Implementation timeline:
- Week 1-2: Complete network assessment and asset identification
- Week 3-4: Define security policies and detection requirements
- Week 5-6: Select technologies and design architecture
- Week 7-10: Deploy sensors and configure initial detection rules
- Week 11-14: Establish baselines and tune alert thresholds
- Week 15-16: Integrate with existing security tools and workflows
- Week 17-20: Train staff and document procedures
- Ongoing: Monitor performance and optimize detection capabilities
Training and Skill Development
Technical staff require adequate training to operate and maintain intrusion detection systems effectively. Training programs should cover system architecture, detection methodologies, alert investigation procedures, and response protocols.
Cross-training multiple team members ensures operational continuity during vacations and staff transitions. For small businesses with limited internal resources, partnering with managed IT service providers can supplement in-house capabilities with expert security monitoring and response services.
Cost-Benefit Analysis and ROI Considerations
Justifying cyber intrusion detection system investments requires demonstrating clear business value beyond general security improvements. Quantifying potential breach costs, regulatory penalties, and operational disruptions helps build compelling business cases for security investments.
The average cost of a data breach continues climbing, with small businesses facing particularly severe impacts relative to their revenue and resources. Early detection significantly reduces breach costs by limiting attacker dwell time and minimizing data exposure.
Financial impact factors:
- Direct breach costs including investigation, notification, and remediation expenses
- Business interruption losses from system downtime and operational disruptions
- Regulatory fines and legal costs from compliance violations
- Reputation damage and customer trust erosion affecting long-term revenue
- Cyber insurance premium reductions for organizations with robust security controls
Measuring Detection Effectiveness
Organizations should establish metrics to evaluate cyber intrusion detection system performance and justify ongoing investments. Key performance indicators include mean time to detect (MTTD), mean time to respond (MTTR), false positive rates, and coverage completeness.
Regular reporting on security incidents detected and prevented demonstrates tangible value to business leadership. Trend analysis showing improving detection capabilities and decreasing incident severity supports continued security program investment.
Implementing a cyber intrusion detection system requires careful planning, appropriate technology selection, and ongoing optimization to achieve effective security monitoring. Small businesses benefit significantly from these capabilities but must balance security requirements with resource constraints and operational realities. If your organization needs expert guidance on deploying intrusion detection capabilities or comprehensive security monitoring services, Delphi Systems Inc. provides managed IT services throughout Lethbridge and surrounding areas with fixed-rate pricing that helps small businesses maintain secure, efficiently managed IT infrastructure.





