Small businesses across Lethbridge and beyond are migrating critical operations to cloud platforms at unprecedented rates. This shift offers remarkable flexibility and cost savings, but it also introduces complex security challenges that demand careful attention. Understanding cloud computing security is no longer optional for organizations that want to protect sensitive data, maintain customer trust, and ensure business continuity in an increasingly digital landscape.
Understanding the Cloud Security Landscape
Cloud computing security encompasses the technologies, policies, and controls deployed to protect data, applications, and infrastructure in cloud environments. Unlike traditional on-premises systems where businesses maintain complete control over physical hardware, cloud security operates under a shared responsibility model that divides security tasks between the service provider and the customer.
This shared responsibility model varies depending on the service type. Infrastructure as a Service (IaaS) providers handle physical security, while customers manage operating systems, applications, and data. Platform as a Service (PaaS) arrangements shift more responsibility to the provider, and Software as a Service (SaaS) solutions place the greatest burden on vendors. According to research highlighted by ITPro, 80% of cloud breaches stem from basic security mistakes, making it essential for businesses to understand exactly where their responsibilities lie.
Key Components of Cloud Security Architecture
A comprehensive cloud computing security strategy addresses multiple layers of protection:
- Identity and Access Management (IAM) controls who can access resources and what actions they can perform
- Data encryption protects information both in transit and at rest
- Network security monitors and filters traffic to prevent unauthorized access
- Compliance management ensures adherence to industry regulations and standards
- Threat detection and response identifies and mitigates security incidents in real time
Small businesses often struggle to implement these components effectively without dedicated IT expertise. The complexity increases when managing multiple cloud platforms simultaneously, as each provider uses different security tools and terminology.

Essential Security Practices for Cloud Environments
Implementing robust cloud computing security requires a systematic approach that addresses vulnerabilities at every level. The Cloud Security Alliance provides comprehensive guidance across twelve critical domains that form the foundation of secure cloud operations.
Access Control and Authentication
Strong authentication mechanisms serve as the first line of defense against unauthorized access. Multi-factor authentication (MFA) should be mandatory for all users accessing cloud resources, particularly for accounts with administrative privileges. Password policies must enforce complexity requirements and regular updates, while privileged access management systems track and control elevated permissions.
Role-based access control (RBAC) ensures users receive only the permissions necessary for their job functions. This principle of least privilege minimizes potential damage from compromised accounts or insider threats. Regular access reviews help identify and remove unnecessary permissions that accumulate over time.
| Authentication Method | Security Level | Implementation Complexity | Cost |
|---|---|---|---|
| Password Only | Low | Low | Minimal |
| MFA (SMS) | Medium | Low | Low |
| MFA (Authenticator App) | High | Medium | Low |
| Hardware Security Keys | Very High | Medium | Moderate |
| Biometric Authentication | Very High | High | High |
Data Protection and Encryption
Every piece of sensitive data moving to the cloud requires encryption protection. Data encryption at rest protects stored information from unauthorized access, while encryption in transit secures data moving between locations. Modern encryption standards like AES-256 provide robust protection that remains computationally infeasible to break with current technology.
Key management presents one of the most challenging aspects of cloud computing security. Businesses must decide whether to use cloud provider key management services or maintain control through their own key management infrastructure. Microsoft’s security best practices emphasize the importance of proper key rotation, secure storage, and access controls for encryption keys.
Data classification helps organizations apply appropriate security controls based on information sensitivity. Public data requires minimal protection, while confidential business information and personally identifiable information (PII) demand stringent security measures. Automated data loss prevention (DLP) tools can identify and protect sensitive data across cloud environments.
Network Security and Segmentation
Cloud network architecture requires careful design to prevent unauthorized lateral movement between resources. Virtual private clouds (VPCs) create isolated network environments within public cloud infrastructure, while security groups and network access control lists filter traffic based on predefined rules.
Implementing Network Segmentation
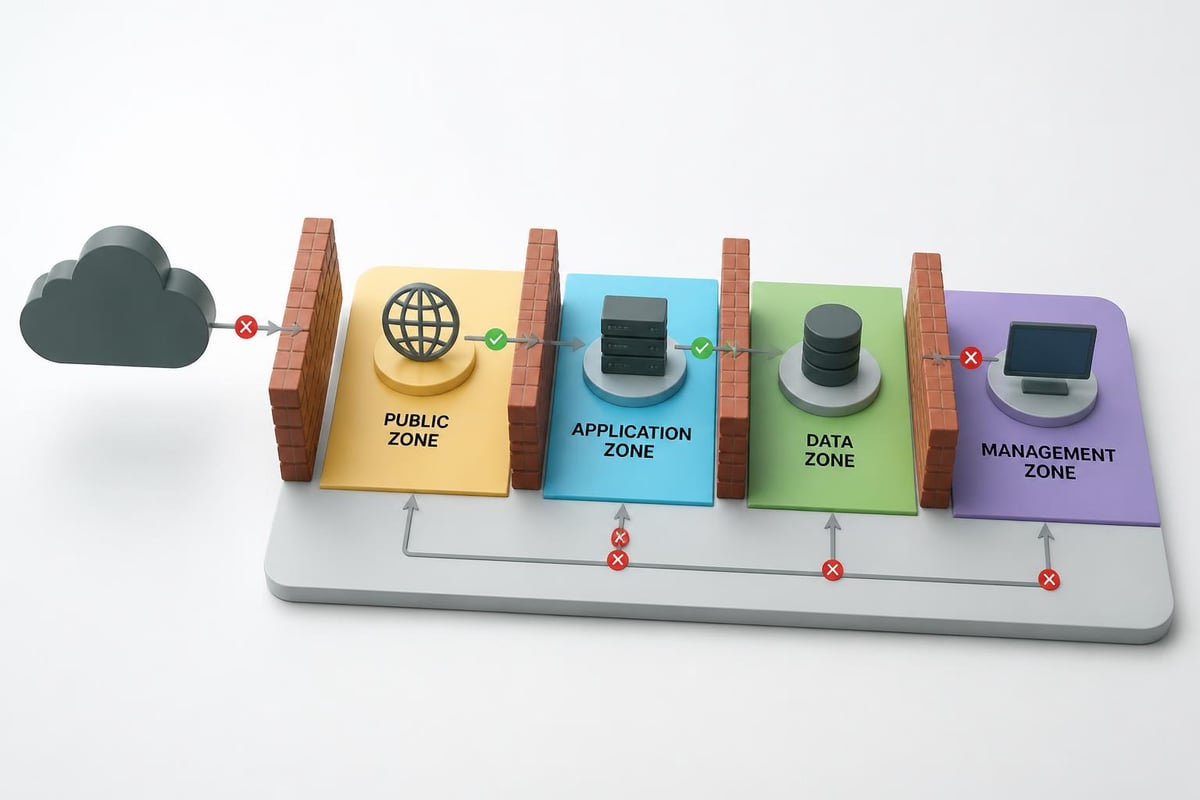
Network segmentation divides cloud infrastructure into distinct zones based on function and security requirements:
- Public-facing zone for web servers and applications accessible from the internet
- Application zone for business logic and processing services
- Data zone for database servers and storage systems
- Management zone for administrative access and monitoring tools
Each zone implements specific security controls appropriate to its risk level. Firewalls between zones enforce strict traffic rules, permitting only necessary communications. This architecture contains potential breaches by limiting an attacker's ability to move freely through the environment.
Web application firewalls (WAFs) protect cloud-hosted applications from common attacks like SQL injection and cross-site scripting. These specialized firewalls analyze HTTP traffic patterns and block malicious requests before they reach application servers. Integration with threat intelligence feeds keeps protection current against emerging attack techniques.
Continuous Monitoring and Threat Detection
Cloud computing security demands constant vigilance through comprehensive monitoring and logging. Cloud platforms generate massive volumes of log data covering user activities, system changes, and network traffic. Security Information and Event Management (SIEM) systems aggregate these logs, correlate events, and identify suspicious patterns that might indicate security incidents.
Automated alert systems notify security teams of potential threats based on predefined rules and behavioral analytics. Machine learning algorithms can detect anomalies that deviate from normal usage patterns, such as unusual login times, unexpected data transfers, or privilege escalation attempts. Early detection enables faster response, often preventing minor security events from escalating into major breaches.
Regular security assessments through vulnerability scanning and penetration testing identify weaknesses before attackers exploit them. Vulnerability scanners automatically check for missing patches, misconfigurations, and known security flaws. Penetration testing simulates real-world attacks to evaluate the effectiveness of security controls and incident response procedures.
Compliance and Regulatory Requirements
Many industries face strict regulatory requirements governing data protection and privacy. Healthcare organizations must comply with HIPAA regulations, while companies handling credit card data follow PCI DSS standards. Financial institutions navigate complex requirements under regulations like GLBA and SOX.
Cloud computing security strategies must incorporate compliance requirements from the planning stage. Documentation proves due diligence and demonstrates adherence to regulatory mandates. Regular compliance audits verify that security controls remain effective and policies stay current with evolving regulations.
- HIPAA requires encryption, access controls, and audit logs for protected health information
- PCI DSS mandates network segmentation, encryption, and regular security testing for payment data
- GDPR enforces data protection principles including purpose limitation and data minimization
- SOC 2 validates controls for security, availability, processing integrity, confidentiality, and privacy
Backup and Disaster Recovery
Cloud computing security extends beyond preventing attacks to ensuring business continuity when incidents occur. Comprehensive backup strategies protect against data loss from security breaches, system failures, or human error. The 3-2-1 backup rule recommends maintaining three copies of data on two different media types with one copy stored offsite.
Cloud-based backup solutions offer automated scheduling, encryption, and geographic redundancy. Regular testing verifies that backups can be restored successfully and within acceptable timeframes. Recovery time objectives (RTO) and recovery point objectives (RPO) define how quickly operations must resume and how much data loss is acceptable.
Disaster recovery planning addresses broader scenarios including complete system failures or regional outages. Multi-region cloud deployments provide redundancy by distributing resources across geographically separated data centers. Failover procedures enable automatic switching to backup systems when primary infrastructure becomes unavailable.
| Recovery Strategy | Recovery Time | Data Loss | Cost | Complexity |
|---|---|---|---|---|
| Backup and Restore | Hours to Days | Hours | Low | Low |
| Pilot Light | Minutes to Hours | Minutes | Medium | Medium |
| Warm Standby | Minutes | Minimal | High | Medium |
| Hot Standby | Seconds | None | Very High | High |
Managing Multi-Cloud Security Challenges
Organizations increasingly adopt multi-cloud strategies to avoid vendor lock-in, optimize costs, and leverage specialized services from different providers. However, managing security across multiple cloud platforms introduces significant complexity that can create dangerous security gaps.
Each cloud provider implements unique security tools, APIs, and management interfaces. Security teams must develop expertise across multiple platforms while maintaining consistent security policies. Cloud security posture management (CSPM) tools help by providing unified visibility and control across hybrid and multi-cloud environments.
Standardizing Security Policies
Consistent security policies across all cloud platforms prevent configuration drift and reduce the risk of overlooked vulnerabilities. Organizations should establish baseline security requirements that apply regardless of the underlying cloud provider:
- Mandatory MFA for all administrative access
- Encryption for all data at rest and in transit
- Network segmentation following the principle of least privilege
- Automated logging and monitoring for security events
- Regular vulnerability scanning and patch management
- Documented incident response procedures
Automation tools can enforce these policies across multiple cloud environments, automatically detecting and remediating policy violations. Infrastructure as Code (IaC) approaches define security configurations in version-controlled templates, ensuring consistent deployment and enabling rapid recovery from misconfigurations.

Security Training and Awareness
Technology controls alone cannot guarantee cloud computing security. Human factors play a critical role in maintaining secure cloud environments. According to security research, social engineering attacks targeting employees remain one of the most effective methods for gaining unauthorized access to cloud resources.
Regular security awareness training helps employees recognize phishing attempts, understand data handling requirements, and follow secure practices. Training should cover cloud-specific topics including proper credential management, identifying suspicious activities, and reporting security concerns. Simulated phishing campaigns test employee awareness and identify areas requiring additional education.
IT staff managing cloud infrastructure need specialized technical training on security features and best practices for specific cloud platforms. Certifications like AWS Certified Security Specialty or Microsoft Certified Azure Security Engineer validate expertise and demonstrate commitment to security excellence. Ongoing education keeps skills current as cloud platforms evolve and new threats emerge.
Vendor Security Assessment
Selecting cloud service providers requires thorough evaluation of their security capabilities and track record. Google Cloud’s security framework demonstrates how leading providers approach security, but businesses must still verify that vendor practices align with their requirements.
Due diligence should examine provider certifications, compliance attestations, and security incident history. SOC 2 Type II reports provide independent validation of security controls, while ISO 27001 certification demonstrates a comprehensive information security management system. Industry-specific certifications like FedRAMP for government work or HITRUST for healthcare add additional assurance.
Service level agreements (SLAs) should clearly define security responsibilities, incident notification timelines, and data handling procedures. Understanding what happens to data during service termination prevents unpleasant surprises when changing providers or discontinuing services. Data portability provisions ensure businesses can retrieve their information in standard formats.
Third-Party Risk Management
Cloud environments often integrate with numerous third-party services and applications. Each integration represents a potential security risk that requires careful management. Third-party risk assessment evaluates vendor security practices, data access requirements, and potential impact of a vendor breach.
Ongoing monitoring tracks third-party security posture through automated feeds and periodic reassessments. Vendor security questionnaires gather information about security controls, while contract provisions establish security requirements and audit rights. Limiting third-party access to only necessary data and systems reduces exposure from vendor compromises.
Cost Optimization Without Compromising Security
Cloud computing security investments must balance protection against budget constraints. Small businesses particularly struggle with this balance, as comprehensive security programs can strain limited resources. Strategic prioritization focuses security spending on the highest-risk areas that protect the most critical assets.
Starting with fundamental controls provides significant protection at reasonable cost. MFA, encryption, and basic monitoring deliver substantial security improvements without requiring expensive specialized tools. As budgets allow, organizations can add more sophisticated capabilities like advanced threat detection and security orchestration.
Managed security service providers offer an alternative to building in-house security expertise. For businesses in Lethbridge and surrounding areas, partnering with local IT service providers delivers professional security management at predictable monthly costs. This approach often proves more economical than hiring dedicated security staff while providing access to broader expertise and 24/7 monitoring capabilities.
Automated security tools reduce operational costs by handling routine tasks without human intervention. Automated patch management, configuration monitoring, and compliance checking free IT staff to focus on strategic security initiatives. Cloud-native security services from providers often include these capabilities at no additional cost beyond compute resources.
Protecting cloud infrastructure requires comprehensive strategies addressing technology, processes, and people across multiple security domains. Small businesses gain significant advantages by implementing systematic cloud computing security practices that prevent costly breaches while enabling safe adoption of cloud technologies. Delphi Systems Inc. helps Lethbridge area businesses navigate these complexities through managed IT services that include expert cloud security, continuous monitoring, and proactive threat management. Our fixed-rate model provides enterprise-grade security without enterprise-level costs, allowing you to focus on growing your business while we ensure your cloud infrastructure remains secure and compliant.




