Small businesses face the same cyber threats as large enterprises, yet often lack the resources to maintain dedicated security teams. Cybercriminals specifically target smaller organizations, recognizing they typically have fewer defenses in place. The solution lies not in building expensive internal security departments, but in partnering with providers who specialize in protecting business networks. This approach offers enterprise-grade protection at a predictable cost, allowing companies to focus on growth while experts handle their security posture around the clock.
Understanding the Modern Threat Landscape
Cyber threats have evolved dramatically in recent years. Ransomware attacks now occur every 11 seconds, with average remediation costs exceeding $1.8 million per incident. Small businesses represent 43% of all cyberattack targets, yet only 14% are adequately prepared to defend themselves.
The most prevalent threats facing small businesses include:
- Ransomware and malware infections
- Phishing and social engineering attacks
- Business email compromise schemes
- Insider threats and credential theft
- Distributed denial of service (DDoS) attacks
- Supply chain vulnerabilities
These threats don't operate in isolation. Modern attackers combine multiple techniques to penetrate defenses, establish persistence, and exfiltrate valuable data before detection occurs. Understanding what managed IT services entail provides crucial context for how comprehensive security fits into broader IT operations.
The Cost of Inadequate Security
Financial losses represent just one dimension of security breaches. Businesses face operational disruption, reputational damage, regulatory penalties, and customer trust erosion. The average downtime following a successful attack spans 21 days, during which revenue generation halts completely.
Recovery extends far beyond restoring systems. Legal fees, forensic investigations, customer notifications, credit monitoring services, and potential lawsuit settlements compound initial losses. For businesses in Lethbridge and surrounding areas, where community relationships form the foundation of success, reputation damage can prove particularly devastating.

What Managed Cybersecurity Solutions Provide
Managed cybersecurity solutions deliver comprehensive protection through continuous monitoring, proactive threat hunting, and rapid incident response. Rather than reacting to breaches after they occur, these services identify and neutralize threats before they cause damage.
Core Service Components
Professional security management encompasses multiple specialized functions working in concert:
| Service Component | Function | Business Benefit |
|---|---|---|
| 24/7 Monitoring | Continuous surveillance of network traffic and system logs | Detects threats outside business hours |
| Threat Intelligence | Real-time updates on emerging attack vectors | Proactive defense against new threats |
| Vulnerability Management | Regular scanning and patch deployment | Closes security gaps before exploitation |
| Incident Response | Rapid containment and remediation | Minimizes damage and recovery time |
| Compliance Support | Policy enforcement and audit assistance | Maintains regulatory requirements |
These components integrate seamlessly, creating defense-in-depth protection that addresses threats at multiple levels. Managed Security Service Providers (MSSPs) specialize in delivering these capabilities with dedicated security operations centers and expert analysts.
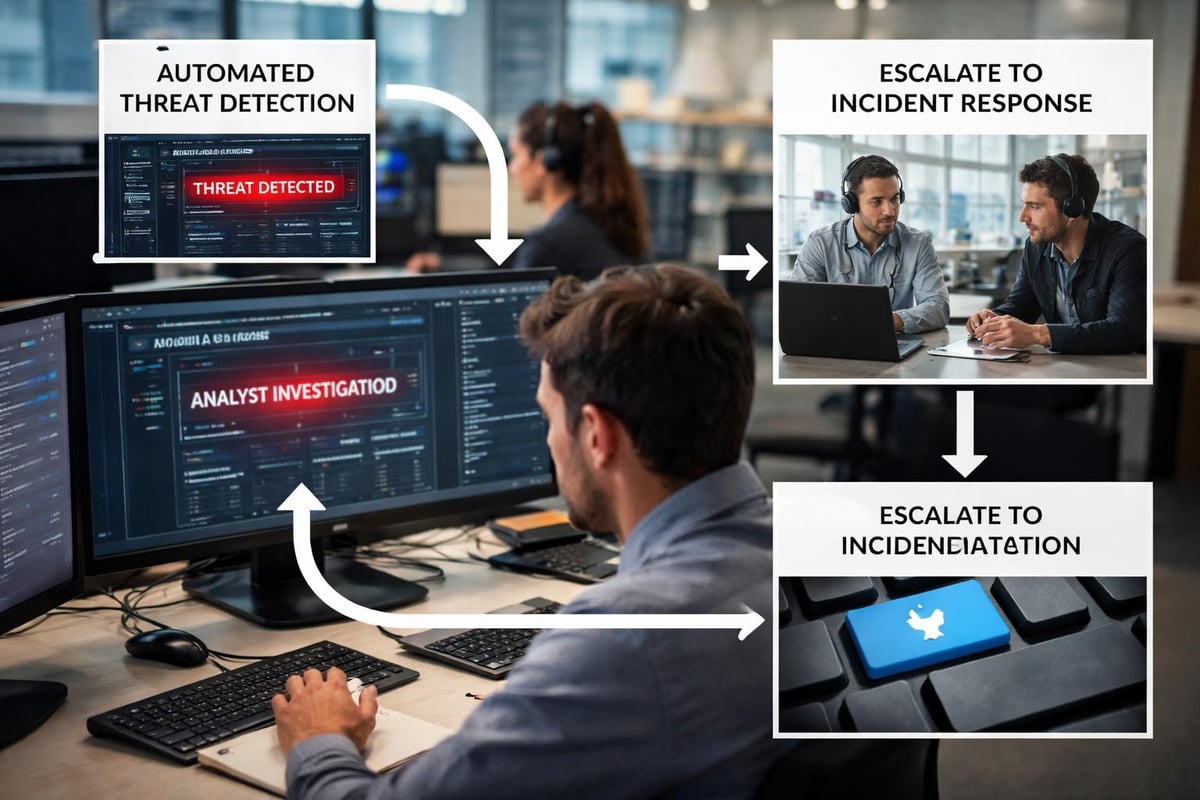
Advanced Detection and Response
Traditional antivirus software no longer provides adequate protection. Managed cybersecurity solutions employ sophisticated detection mechanisms that identify suspicious behavior patterns rather than relying solely on known threat signatures.
Modern detection capabilities include:
- Behavioral analytics identifying anomalous user activity
- Network traffic analysis spotting command and control communications
- Endpoint detection and response (EDR) monitoring individual devices
- Security information and event management (SIEM) correlating data across systems
- Threat hunting proactively searching for hidden adversaries
This multi-layered approach catches threats that evade traditional security tools. When detection occurs, managed security teams respond immediately, containing threats before they spread throughout the network.
Benefits for Small Business Operations
Implementing managed cybersecurity solutions transforms security from a cost center into a strategic advantage. Businesses gain capabilities previously available only to large enterprises with substantial IT budgets.
Predictable Investment Structure
Fixed monthly fees replace unpredictable security expenses. This pricing model eliminates the financial uncertainty of hiring full-time security staff, purchasing expensive tools, and responding to emergency incidents. Small businesses can budget confidently, knowing security costs remain stable regardless of threat volume.
The alternative approach carries hidden costs. Building internal security capabilities requires recruiting specialized talent in a competitive market, investing in multiple security platforms, maintaining tool licenses, and continuous training to keep pace with evolving threats. For most small businesses, these expenses far exceed managed service costs.
Access to Specialized Expertise
Security professionals require years of training and experience to effectively defend against sophisticated threats. The global cybersecurity skills gap exceeds 3.4 million positions, making qualified talent difficult to attract and retain.
Managed cybersecurity solutions provide access to entire teams of specialists with diverse expertise. These teams include:
- Security analysts monitoring systems around the clock
- Incident responders trained in containment and remediation
- Compliance experts understanding regulatory requirements
- Network architects designing secure infrastructure
- Threat intelligence researchers tracking emerging dangers
This depth of knowledge proves impossible for individual businesses to replicate internally. Teams stay current through continuous training, certification programs, and exposure to threats across multiple client environments.
Key Features of Effective Security Management
Not all managed cybersecurity solutions deliver equal value. Distinguishing characteristics separate adequate services from exceptional protection.
Proactive Threat Prevention
Superior providers don't simply react to detected threats. They actively strengthen defenses through regular vulnerability assessments, security awareness training, and policy development. This proactive stance addresses weaknesses before attackers discover them.
Vulnerability management follows a continuous cycle:
- Automated scanning identifies system weaknesses
- Risk assessment prioritizes remediation based on threat likelihood
- Patch deployment closes security gaps systematically
- Verification testing confirms successful remediation
- Documentation maintains compliance audit trails
This systematic approach reduces attack surface area while maintaining operational stability. Patches deploy during maintenance windows to minimize business disruption.
Comprehensive Visibility and Reporting
Effective security management provides transparency into protection status. Regular reports demonstrate security posture, highlight addressed threats, and identify areas requiring attention.
| Report Type | Frequency | Content |
|---|---|---|
| Executive Summary | Monthly | High-level security status and key metrics |
| Technical Analysis | Weekly | Detailed threat activity and response actions |
| Compliance Audit | Quarterly | Regulatory requirement adherence status |
| Incident Reports | As Needed | Specific threat investigations and outcomes |
This visibility enables informed decision-making about security investments and risk tolerance. Business leaders understand protection levels without requiring technical expertise.
Integration with Existing Infrastructure
Managed cybersecurity solutions must work seamlessly with current technology environments. Providers supporting diverse platforms, applications, and network configurations deliver superior value compared to those requiring extensive infrastructure changes.
Modern security tools integrate through application programming interfaces (APIs), allowing centralized management across disparate systems. This interoperability extends protection to cloud services, mobile devices, and remote work environments without creating management complexity.
Implementation Considerations for Small Businesses
Selecting and deploying managed cybersecurity solutions requires careful planning to ensure maximum protection value.
Assessing Current Security Posture
Implementation begins with comprehensive security assessments identifying existing vulnerabilities, compliance gaps, and protection deficiencies. These evaluations establish baselines for measuring improvement and prioritizing remediation efforts.
Assessment components typically include:
- Network architecture review examining security controls
- Vulnerability scanning across all systems and applications
- Policy evaluation comparing practices against industry standards
- User access audit identifying excessive permissions
- Incident response capability testing through tabletop exercises
Results inform customized security strategies addressing specific business risks rather than applying generic solutions.
Transition Planning and Onboarding
Smooth transitions minimize disruption while establishing comprehensive protection. Effective providers develop detailed implementation roadmaps outlining phases, timelines, and responsibilities.
Typical onboarding phases include:
- Discovery and Planning (Week 1-2): Document infrastructure, define requirements, establish success metrics
- Tool Deployment (Week 3-4): Install monitoring agents, configure security platforms, establish connectivity
- Tuning and Optimization (Week 5-6): Adjust detection thresholds, reduce false positives, customize alerts
- Training and Handoff (Week 7-8): Educate internal staff, establish communication protocols, finalize procedures
This structured approach ensures thorough protection without overwhelming business operations. Building security-first frameworks requires integrating security considerations throughout the technology stack.

Ongoing Partnership and Evolution
Security requirements change as businesses grow and threats evolve. Effective managed cybersecurity solutions adapt through regular strategy reviews, capability enhancements, and technology updates.
Quarterly business reviews assess protection effectiveness, discuss emerging risks, and align security investments with business objectives. This collaborative approach ensures security strategies support rather than hinder business growth.
Providers staying ahead of threat evolution deliver sustained value. MSP security must evolve continuously to address increasingly sophisticated attack techniques and expanding attack surfaces.
Evaluating Managed Security Providers
Choosing the right partner significantly impacts security outcomes. Several critical factors distinguish superior providers from adequate alternatives.
Industry Experience and Specialization
Providers with deep experience in specific industries understand unique compliance requirements, common threat vectors, and operational constraints. This specialized knowledge accelerates deployment and improves protection effectiveness.
Small businesses benefit particularly from providers familiar with resource constraints and practical security challenges. Providers serving similar organizations bring proven strategies rather than requiring costly trial-and-error approaches.
Technology Stack and Capabilities
Modern threats require advanced detection and response technologies. Evaluate providers based on their security tool investments and technical capabilities.
Essential technology components include:
- Next-generation firewalls with deep packet inspection
- Endpoint detection and response platforms
- Security information and event management systems
- Email security and anti-phishing tools
- Vulnerability scanning and patch management automation
- Backup and disaster recovery solutions
Integration quality matters as much as individual tool capabilities. Seamless data sharing between platforms enables comprehensive threat correlation and faster response.
Service Level Agreements and Response Times
Clear service level agreements (SLAs) establish performance expectations and accountability measures. These contracts should specify response times, availability guarantees, and remediation commitments.
| Severity Level | Initial Response | Resolution Target | Escalation Protocol |
|---|---|---|---|
| Critical | 15 minutes | 2 hours | Immediate executive notification |
| High | 1 hour | 4 hours | Manager notification within 30 minutes |
| Medium | 4 hours | 24 hours | Standard escalation after 8 hours |
| Low | 8 hours | 5 business days | Escalation if timeline exceeded |
These commitments ensure urgent threats receive immediate attention while routine matters follow efficient workflows.
Geographic Presence and Local Support
While security monitoring occurs remotely, local presence provides significant advantages. Providers familiar with regional business environments, regulatory requirements, and community dynamics deliver more relevant guidance.
For businesses operating in Lethbridge and surrounding areas, working with providers who understand Western Canadian business culture, provincial regulations, and local threat patterns enhances service quality. On-site support capabilities enable faster response to situations requiring physical presence.
Compliance and Regulatory Considerations
Many industries face specific cybersecurity compliance requirements. Managed cybersecurity solutions help navigate these complex regulatory landscapes while maintaining business flexibility.
Common Compliance Frameworks
Different industries follow various security standards and regulations:
- Healthcare: PIPEDA (Personal Information Protection and Electronic Documents Act)
- Financial Services: OSFI Cyber Security Self-Assessment, PCI DSS
- Professional Services: Provincial privacy legislation, professional body requirements
- General Business: Privacy legislation, contractual security requirements
Managed security providers familiar with these frameworks implement appropriate controls, maintain documentation, and support audit processes. This expertise prevents costly compliance violations and simplifies regulatory interactions.
Documentation and Audit Support
Compliance requires extensive documentation demonstrating security controls, incident responses, and policy enforcement. Managed providers maintain these records systematically, producing audit-ready reports demonstrating regulatory adherence.
Regular compliance assessments identify gaps before regulators or auditors discover them. Remediation plans address deficiencies systematically while maintaining operational continuity.
Integration with Broader IT Strategy
Security functions most effectively when integrated with comprehensive IT management rather than operating as an isolated function. Managed cybersecurity solutions should complement broader technology strategies supporting business objectives.
Holistic Technology Management
Effective IT operations combine security, infrastructure management, cloud services, backup solutions, and user support into cohesive frameworks. This integration eliminates gaps between different technology domains while improving efficiency.
When working with Delphi Systems Inc., small businesses gain unified management across all IT functions, ensuring security considerations inform every technology decision. This comprehensive approach prevents situations where infrastructure changes inadvertently create security vulnerabilities.
Scalability and Future Growth
Technology solutions must accommodate business expansion without requiring complete redesigns. Managed cybersecurity solutions should scale seamlessly as organizations add employees, locations, and technology platforms.
Cloud-based security tools particularly support growth by eliminating capacity constraints associated with on-premises hardware. Protection extends automatically to new resources without manual configuration or additional infrastructure investments.
Employee Training and Security Culture
Technology alone cannot prevent all security incidents. Human factors contribute to 95% of cybersecurity breaches, making employee education essential for comprehensive protection.
Security Awareness Programs
Effective managed cybersecurity solutions include regular security awareness training covering common threats and safe computing practices. Training topics should address:
- Phishing email identification and reporting procedures
- Password security and multi-factor authentication usage
- Safe internet browsing and download practices
- Mobile device security for remote work
- Social engineering recognition and response
- Data handling and privacy protection
Interactive training with realistic simulations proves more effective than generic presentations. Regular phishing simulations identify vulnerable employees while reinforcing safe email practices.
Building Security-Conscious Culture
Sustainable security requires organizational culture where employees view protection as shared responsibility rather than IT department obligation. Managed providers support this cultural shift through executive engagement, clear communication, and positive reinforcement.
Recognition programs celebrating employees who identify and report suspicious activity encourage vigilant behavior. Incident response plans should emphasize learning rather than blame, creating safe environments for reporting potential compromises.
Measuring Security Investment Return
Business leaders rightfully expect measurable returns from security investments. Effective managed cybersecurity solutions demonstrate value through multiple metrics beyond simple cost avoidance.
Quantifiable Security Metrics
Track improvement across key security indicators:
- Mean Time to Detect (MTTD): Average duration between threat occurrence and detection
- Mean Time to Respond (MTTR): Average response time from detection to containment
- Vulnerability Remediation Rate: Percentage of identified weaknesses addressed within target timeframes
- Security Incident Frequency: Number of successful compromises over specified periods
- Compliance Audit Results: Findings and deficiency trends across regulatory assessments
These metrics demonstrate security program maturity and continuous improvement. Declining detection times and incident frequencies indicate strengthening defenses.
Business Impact Measurements
Security investments should support broader business objectives beyond pure risk reduction:
- Productivity Gains: Reduced downtime and faster incident recovery
- Customer Confidence: Enhanced reputation supporting sales and retention
- Competitive Advantage: Security certifications differentiating from competitors
- Insurance Cost Reduction: Lower premiums from demonstrated security practices
- Operational Efficiency: Automated security processes reducing manual intervention
These business benefits often exceed direct cost savings from prevented incidents, justifying security investments through multiple value streams.
Managed cybersecurity solutions provide small businesses with enterprise-grade protection against evolving threats while maintaining predictable costs and operational focus. By partnering with experienced providers, organizations gain specialized expertise, advanced technologies, and continuous monitoring that would prove prohibitively expensive to build internally. Delphi Systems Inc. delivers comprehensive managed IT services including robust cybersecurity protection for businesses throughout Lethbridge and surrounding areas, combining local expertise with advanced security capabilities to keep your operations secure and productive. Contact us today to learn how our fixed-rate managed services can strengthen your security posture while allowing you to focus on growing your business.





