The digital landscape continues to evolve at an unprecedented pace, and for small businesses in Lethbridge and beyond, understanding the relationship between network infrastructure and security has never been more critical. Networking in cyber security represents the intersection where data transmission meets threat protection, creating a complex yet essential framework that keeps business operations running safely. As cyber threats become increasingly sophisticated, business owners must grasp how their network architecture directly influences their vulnerability to attacks, data breaches, and operational disruptions.
Understanding Network Fundamentals in Security Context
Network infrastructure forms the backbone of modern business operations, and every connection point represents both an opportunity and a potential vulnerability. When examining networking in cyber security, professionals recognize that networking fundamentals establish the foundation of cybersecurity practices across organizations of all sizes.
Core Network Components and Their Security Implications
Small businesses typically operate on network architectures consisting of several critical components. Routers direct traffic between different networks, switches connect devices within a local area network (LAN), and firewalls serve as protective barriers against unauthorized access. Each component requires specific security configurations to function effectively within a protected environment.
Key network devices include:
- Routers: Direct data packets between networks and enforce access control lists (ACLs)
- Switches: Connect devices within LANs and can implement VLAN segmentation
- Firewalls: Filter incoming and outgoing traffic based on security rules
- Access points: Provide wireless connectivity with encryption protocols
- Network attached storage: Centralize data with backup capabilities
Understanding these components allows business owners to make informed decisions about security investments. A properly configured router with updated firmware provides the first line of defense, while network switches with VLAN capabilities enable traffic segmentation that limits lateral movement during security incidents.

Protocol Security and Traffic Management
The language that devices use to communicate across networks relies on standardized protocols, each with distinct security characteristics. Networking in cyber security requires deep familiarity with how protocols function and where vulnerabilities commonly emerge within network communications.
Essential Protocols and Their Vulnerabilities
| Protocol | Primary Function | Security Considerations | Protection Methods |
|---|---|---|---|
| TCP/IP | Data transmission foundation | Susceptible to spoofing, session hijacking | Encryption, VPNs, firewall rules |
| DNS | Domain name resolution | DNS poisoning, tunneling attacks | DNSSEC, monitoring, filtering |
| HTTP/HTTPS | Web communication | Man-in-the-middle attacks (HTTP only) | SSL/TLS certificates, HTTPS enforcement |
| SMTP | Email transmission | Spam, phishing, malware delivery | Authentication, filtering, encryption |
| FTP/SFTP | File transfer | Unencrypted transmission (FTP) | SFTP, FTPS with encryption |
The transition from HTTP to HTTPS demonstrates how protocol evolution addresses security needs. Small businesses must ensure their websites and applications utilize encrypted protocols to protect customer data during transmission. Understanding networking protocols and their applications in cybersecurity helps organizations identify where encrypted alternatives should replace legacy systems.
Port management represents another critical aspect of protocol security. Services listen on specific ports, and open ports create potential entry points for attackers. Regular port scanning and proper firewall configuration ensure that only necessary services remain accessible from external networks.
Network Segmentation and Access Control
Effective network design separates different types of traffic and user groups through segmentation strategies. This architectural approach significantly enhances security by containing potential breaches and limiting unauthorized access to sensitive resources.
Implementing VLANs for Security Enhancement
Virtual Local Area Networks (VLANs) provide logical separation of network traffic without requiring separate physical infrastructure. For small businesses, VLAN implementation offers cost-effective security improvements through traffic isolation.
- Identify segmentation requirements based on business functions and data sensitivity
- Create VLANs for distinct purposes such as guest WiFi, employee workstations, servers, and IoT devices
- Configure inter-VLAN routing rules to control communication between segments
- Implement access control lists that specify allowed traffic flows
- Monitor VLAN traffic patterns for unusual activity indicating potential compromises
A typical small business might establish separate VLANs for administrative systems, customer-facing services, and general employee access. This separation ensures that a compromised employee workstation cannot directly access sensitive financial systems or customer databases.
Access control extends beyond VLAN configuration to include user authentication and authorization mechanisms. Network access control (NAC) solutions verify device compliance with security policies before granting network connectivity, ensuring that outdated or infected devices remain isolated from production systems.
Monitoring and Intrusion Detection
Visibility into network traffic patterns enables early detection of security incidents and anomalous behavior. Networking in cyber security emphasizes continuous monitoring as a cornerstone of effective defense strategies.
Network Monitoring Tools and Techniques
Modern monitoring solutions provide real-time insights into traffic flows, bandwidth utilization, and security events. Small businesses benefit from implementing monitoring capabilities that match their technical resources and security requirements.
Essential monitoring components include:
- Traffic analysis tools that identify unusual patterns
- Intrusion detection systems (IDS) that recognize attack signatures
- Intrusion prevention systems (IPS) that automatically block threats
- Security information and event management (SIEM) platforms for log aggregation
- Network behavior analysis that establishes baseline activity
The distinction between intrusion detection and prevention lies in their response mechanisms. IDS solutions alert administrators to suspicious activity, while IPS systems actively block detected threats. For businesses with limited IT staff, managed security services provide expertise in monitoring and response without requiring internal specialists.
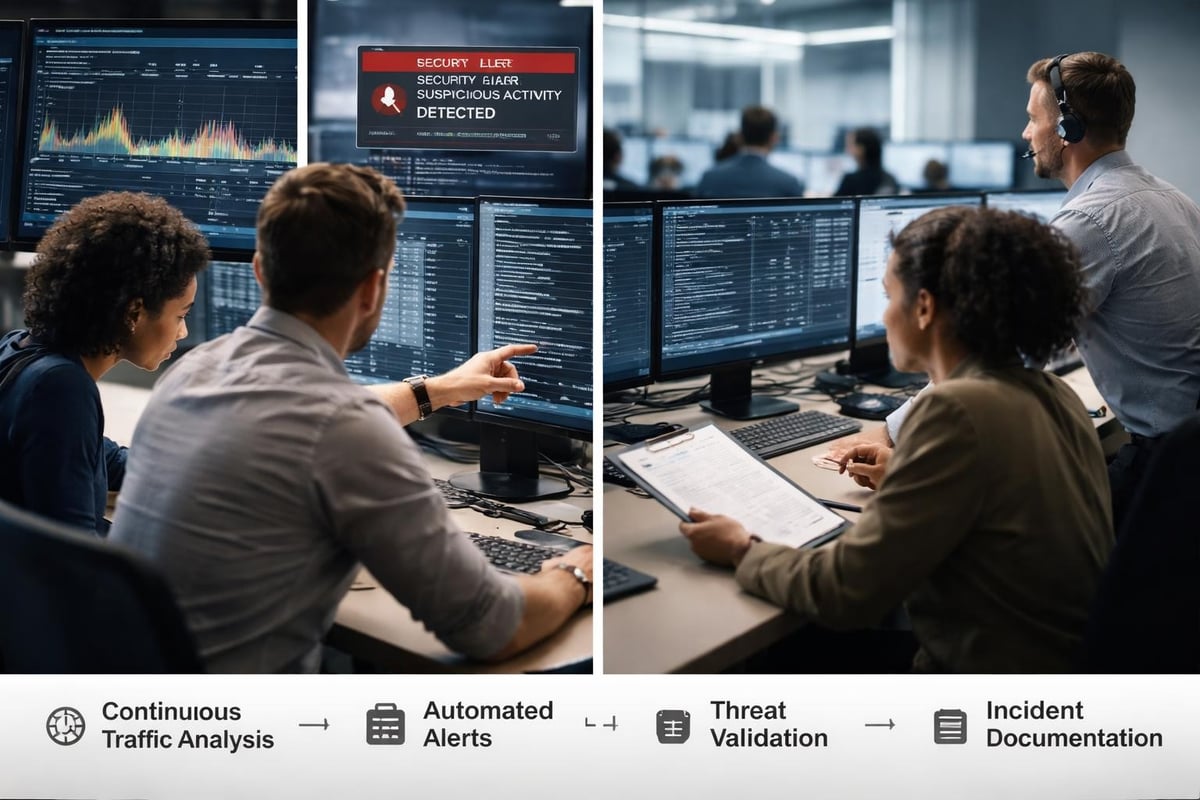
Logging plays a crucial role in both real-time monitoring and forensic investigation. Comprehensive logs capture authentication attempts, configuration changes, and traffic patterns that help reconstruct security incidents. Retention policies must balance storage costs against compliance requirements and investigative needs.
Wireless Network Security Considerations
WiFi networks present unique security challenges due to their broadcast nature and accessibility. The importance of networking in cyber security becomes particularly evident when examining wireless vulnerabilities and protection mechanisms.
Securing Wireless Access Points
| Security Feature | Purpose | Implementation Priority |
|---|---|---|
| WPA3 Encryption | Protect transmitted data | Critical |
| Strong Pre-Shared Keys | Prevent unauthorized access | Critical |
| SSID Broadcasting Control | Reduce visibility to attackers | Moderate |
| MAC Address Filtering | Limit device connections | Low (easily spoofed) |
| Guest Network Isolation | Separate visitor traffic | High |
| Regular Firmware Updates | Patch vulnerabilities | Critical |
Modern wireless security relies on WPA3 encryption, which addresses weaknesses found in earlier WPA2 implementations. Businesses should audit their wireless infrastructure to ensure legacy protocols are disabled and only current security standards remain active.
Guest network implementation deserves special attention in small business environments. Providing WiFi access to customers or visitors through isolated networks prevents potentially compromised devices from accessing internal resources. This segmentation protects business systems while maintaining customer convenience.
Cloud Integration and Hybrid Network Security
The shift toward cloud services transforms traditional network perimeters and introduces new security considerations. Networking in cyber security must account for data flowing between on-premises infrastructure and cloud platforms, creating hybrid environments with expanded attack surfaces.
Securing Cloud Connections
Virtual Private Networks (VPNs) establish encrypted tunnels between remote locations and central resources. Site-to-site VPNs connect branch offices or cloud environments, while remote access VPNs enable secure connections for individual users working from various locations.
- Evaluate VPN protocols for security and performance characteristics
- Implement multi-factor authentication for VPN access
- Configure split tunneling policies based on security requirements
- Monitor VPN connection logs for unauthorized access attempts
- Maintain updated VPN client software across all devices
Cloud access security brokers (CASBs) provide visibility and control over cloud service usage. These solutions sit between users and cloud applications, enforcing security policies and detecting risky activities. For small businesses utilizing multiple cloud services, CASBs offer centralized management of previously disparate security controls.
Direct connections to cloud providers through dedicated circuits bypass the public internet, reducing exposure to certain attack vectors. While more expensive than VPN connections, dedicated circuits provide consistent performance and enhanced security for businesses with significant cloud dependencies.
Network Vulnerability Assessment
Regular security assessments identify weaknesses before attackers exploit them. Building blocks of networking in the cybersecurity industry include systematic evaluation of network defenses through various assessment methodologies.
Penetration Testing and Vulnerability Scanning
Vulnerability scanning automates the detection of known security weaknesses across network devices and systems. These tools compare device configurations and software versions against databases of known vulnerabilities, generating reports that prioritize remediation efforts based on risk severity.
Penetration testing goes beyond automated scanning by simulating real-world attack scenarios. Skilled testers attempt to exploit identified vulnerabilities, demonstrating actual risk and potential impact. Small businesses benefit from annual penetration tests that validate security controls and reveal gaps in defensive measures.
Assessment frequency guidelines:
- Automated vulnerability scanning: Weekly or monthly
- Internal security audits: Quarterly
- Penetration testing: Annually or after major infrastructure changes
- Configuration reviews: Bi-annually
- Compliance assessments: Based on regulatory requirements
Results from these assessments inform security roadmaps and budget allocation. Prioritizing remediation based on actual business risk ensures limited resources address the most critical vulnerabilities first.

Incident Response and Network Forensics
Despite preventive measures, security incidents occur, and effective response capabilities minimize damage and recovery time. Networking in cyber security includes planning for network-based attacks and developing response procedures that restore normal operations quickly.
Developing Network Incident Response Plans
Incident response plans document procedures for detecting, containing, and recovering from security events. Network-specific components address traffic redirection, system isolation, and evidence preservation for forensic analysis.
Response teams require tools and authority to act decisively during incidents. Network diagrams, contact lists, and predefined response procedures reduce confusion during high-pressure situations. Regular tabletop exercises test plan effectiveness and identify gaps before real incidents occur.
Network forensics involves capturing and analyzing traffic data to understand attack methods and scope. Packet capture tools preserve network communications for detailed examination, while flow data provides high-level visibility into connection patterns. Both data types contribute valuable evidence during investigations and legal proceedings.
Emerging Threats and Adaptive Security
The threat landscape continuously evolves as attackers develop new techniques and exploit emerging technologies. Small businesses must adapt their networking in cyber security strategies to address contemporary risks without overextending limited resources.
Zero Trust Network Architecture
Traditional perimeter-based security assumes internal network traffic is trustworthy, but modern threats frequently originate from compromised internal systems. Zero trust architecture eliminates this assumption by requiring continuous verification for all users and devices regardless of location.
Implementing zero trust principles involves several fundamental shifts:
- Verify explicitly using multiple authentication factors
- Apply least privilege access for all users and systems
- Assume breach and segment networks to contain incidents
- Inspect and log all traffic regardless of source
- Enforce encryption for data in transit and at rest
While full zero trust implementation requires significant effort, small businesses can adopt incremental approaches that improve security posture progressively. Starting with multi-factor authentication and network segmentation provides immediate benefits while building toward comprehensive zero trust capabilities.
Network Security Training and Awareness
Technical controls provide essential protection, but human factors remain critical in network security. Employees who understand basic networking concepts and security principles become active participants in organizational defense rather than potential vulnerabilities.
Building Security-Conscious Culture
Training programs should address network security topics relevant to employee roles. General staff need awareness of phishing risks, safe browsing practices, and incident reporting procedures. IT personnel require deeper technical knowledge covering networking basics for cybersecurity including protocol security and threat detection.
Regular security communications keep network protection top of mind. Brief updates about emerging threats, security wins, and improvement initiatives demonstrate organizational commitment to cybersecurity. Recognition programs that reward security-conscious behavior reinforce desired actions across the workforce.
Compliance and Regulatory Considerations
Industry regulations and data protection laws impose specific network security requirements on businesses handling sensitive information. Understanding applicable compliance frameworks ensures network designs meet legal obligations while protecting organizational interests.
Common Compliance Requirements
| Framework | Key Network Security Requirements | Applicable Organizations |
|---|---|---|
| PCI DSS | Network segmentation, encryption, access controls | Businesses processing credit cards |
| HIPAA | Encrypted transmission, audit logging, access restrictions | Healthcare providers and partners |
| GDPR | Data protection by design, breach notification, international transfer controls | Organizations handling EU resident data |
| SOC 2 | Security monitoring, change management, incident response | Service providers with customer data |
Compliance frameworks typically mandate regular security assessments, documented policies, and evidence of control effectiveness. Maintaining compliance requires ongoing effort rather than one-time certification, making automated monitoring and reporting capabilities valuable investments.
Network documentation supports compliance efforts by demonstrating security control implementation. Current network diagrams, firewall rule sets, and access control matrices provide auditors with evidence of proper security measures. Delphi Systems Inc. helps businesses maintain this documentation as part of comprehensive managed IT services.
Balancing Security and Performance
Network security measures inevitably impact performance, and finding appropriate balance requires understanding business priorities and user requirements. Overly restrictive controls frustrate legitimate users and may drive workarounds that undermine security, while insufficient protection exposes organizations to unacceptable risks.
Optimizing Security Controls
Deep packet inspection provides thorough traffic analysis but increases latency compared to stateful firewall inspection. Encryption protects data confidentiality while adding processing overhead. Organizations must calibrate security measures based on actual risk profiles and performance requirements.
Testing security controls under realistic conditions reveals performance impacts before production deployment. Baseline measurements establish normal network performance, while controlled testing of new security tools quantifies their effects. This data-driven approach supports informed decisions about security investments and configurations.
Quality of Service (QoS) policies prioritize critical traffic when bandwidth limitations create congestion. By classifying traffic types and allocating appropriate bandwidth, QoS ensures that security controls do not interfere with essential business communications. Voice and video traffic particularly benefit from QoS prioritization that maintains quality despite network security processing.
Effective networking in cyber security requires understanding how network infrastructure, protocols, and security controls work together to protect business operations while enabling productivity. Small businesses that invest in proper network design, monitoring, and security measures position themselves to defend against evolving threats while maintaining the reliable connectivity their operations demand. Delphi Systems Inc. provides comprehensive managed IT services throughout Lethbridge and surrounding areas, delivering expert network security implementation and ongoing monitoring that keeps your business protected without diverting resources from core activities.





