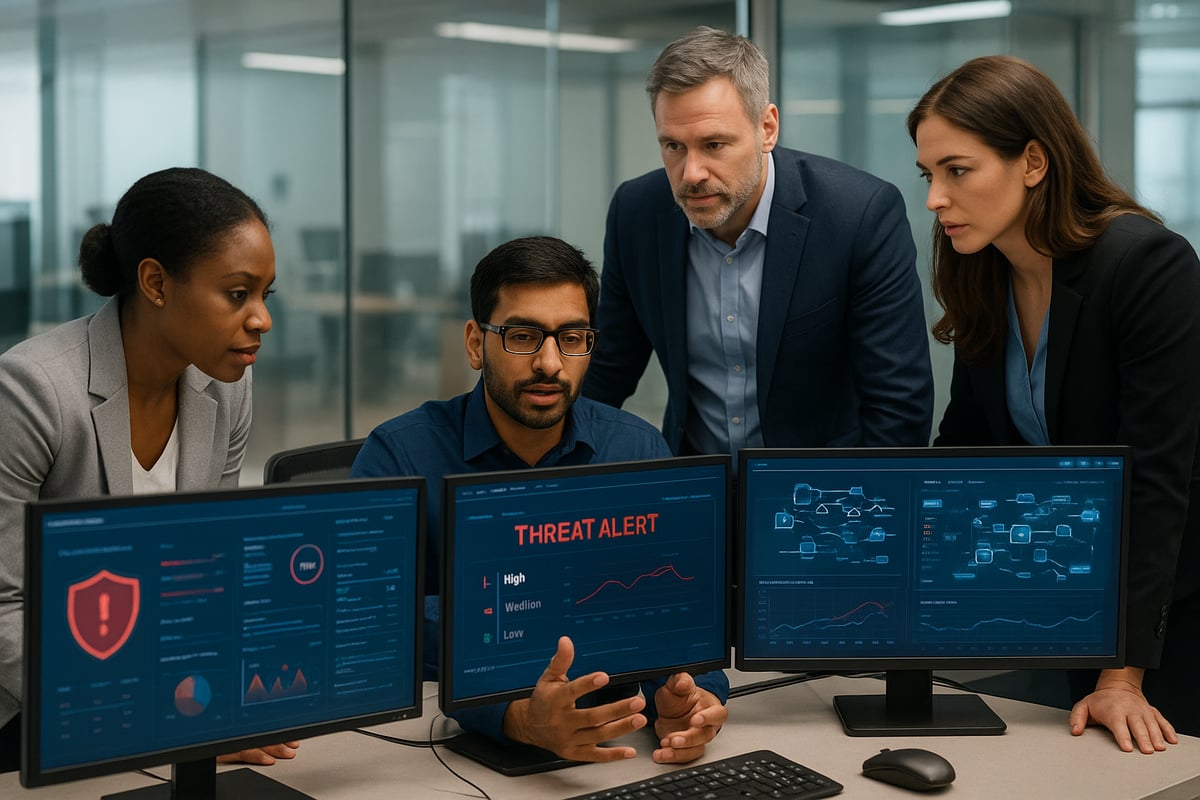
By 2026, cyberattacks against businesses are projected to rise by more than 40%, impacting organizations of every size. The risk of data breaches, ransomware attacks, and sophisticated digital threats has never been higher.
Today, business network security is essential for protecting operations, reputation, and meeting regulatory demands. Without proactive defenses, companies face disruptions and costly penalties.
This guide offers actionable strategies to help you future-proof your network. Explore core concepts, the evolving threat landscape, must-have security measures, technology trends, compliance essentials, and practical steps for securing your business network in 2026.
Understanding Business Network Security in 2026
Modern business network security is the foundation of organizational resilience. It protects sensitive data, systems, and resources from unauthorized access and a constantly evolving array of cyber threats. Today, the complexity of business network security is increasing, driven by remote work, the Internet of Things, and widespread cloud adoption.

Defining Business Network Security
Business network security involves deploying a layered defense to shield data, systems, and resources from cyber threats. This approach includes hardware safeguards, software solutions, strict policies, and vigilant user practices. As more organizations embrace remote work, IoT devices, and cloud services, business network security must adapt to new challenges.
For example, small businesses with fewer than 1,000 employees accounted for 46 percent of data breaches recently. This statistic highlights how vital comprehensive and flexible business network security measures are for companies of all sizes.
The Evolving Threat Landscape
The threat landscape facing business network security is growing more sophisticated each year. Attackers use ransomware, phishing, supply chain exploits, and advanced persistent threats to breach defenses. With the number of endpoints and remote access points multiplying, new vulnerabilities emerge constantly.
Credential-based attacks are especially alarming, with credential theft surged 160% in 2025. Notably, 82 percent of ransomware attacks now target businesses with fewer than 1,000 employees. High-profile breaches affecting both small and large organizations reinforce the need for robust business network security.
The Business Impact of Network Breaches
Network breaches have far-reaching consequences for business network security. Reputational damage, financial loss, legal penalties, and operational disruption can cripple an organization. Up to 60 percent of small businesses fail within six months of a major cyberattack.
Certain industries, such as healthcare, finance, and retail, face even higher risks due to sensitive data and strict regulations. Regulatory frameworks like GDPR, NIS2, and HIPAA impose heavy fines for non-compliance, compounding the impact of weak business network security.
Key Security Principles for 2026
To meet the demands of 2026, business network security should focus on Zero Trust, least privilege, and continuous monitoring. Defense-in-depth strategies and security by design are essential, ensuring that protection is built into every layer.
User education remains a critical frontline defense for business network security. As organizations grow and technology evolves, adaptable and scalable solutions will be necessary to stay ahead of emerging threats and maintain resilience.
Core Strategies for Business Network Security
Effective business network security in 2026 requires a blend of proven techniques and modern innovations. By adopting a layered approach, businesses can address threats at every level, from user identities to remote endpoints. Let’s explore seven core strategies that form the backbone of a resilient security posture.
1. Identity and Access Management (IAM)
Robust identity and access management is fundamental to business network security. Centralized IAM platforms such as Azure AD, Okta, or JumpCloud streamline user provisioning and deprovisioning. Enforcing strong password policies and conducting regular credential reviews help prevent unauthorized access.
- Implement Single Sign-On for efficiency.
- Automate onboarding and offboarding processes.
- Integrate with multi-factor authentication and conditional access.
Regularly removing stale accounts significantly reduces attack surface. IAM ensures only the right people have access to sensitive resources, adapting as the business evolves.
2. Multi-Factor Authentication (MFA) Everywhere
Multi-factor authentication is essential for business network security, providing a crucial barrier against account compromise. MFA should be mandatory for all users, devices, and remote access points.
- Deploy emerging MFA methods like biometrics and hardware tokens.
- Use FIDO2 standards for enhanced protection.
- Address user adoption with clear communication and training.
Studies show MFA can prevent up to 99.9% of account-based attacks. Rolling out MFA across the organization, while supporting users, strengthens defenses without sacrificing usability.
3. Network Segmentation and Zero Trust Architecture
Network segmentation and Zero Trust principles are central to business network security. By dividing networks by department, role, or sensitivity, you minimize the blast radius of a breach.
- Apply micro-segmentation to isolate assets.
- Use software-defined perimeters for dynamic access control.
- Enforce policies that verify every connection.
Limiting lateral movement makes it harder for attackers to escalate privileges. Zero Trust means no implicit trust, continuously validating every access attempt for enhanced protection.
4. Endpoint Security and Device Posture Management
Endpoints are frequent targets, making their protection vital to business network security. Deploying advanced endpoint detection and response (EDR/XDR) solutions ensures all devices are monitored and secured.
- Enforce full-disk encryption on laptops and mobiles.
- Patch systems frequently to close vulnerabilities.
- Check device posture for compliance before granting access.
Unpatched devices are a leading cause of breaches. Centralized dashboards offer visibility and control, enabling rapid response to threats and maintaining a strong security baseline.
5. Secure Remote Access Solutions
With hybrid and remote work the norm, secure remote access is a pillar of business network security. Legacy VPNs should be replaced with technologies like Zero Trust Network Access (ZTNA) and SD-WAN.
- Grant least privilege and contextual access.
- Monitor and log all remote sessions for anomalies.
- Use cloud-delivered VPNs and secure gateways for flexibility.
These solutions ensure compliance with remote work policies and reduce the risk of unauthorized entry, supporting productivity without compromising safety.
6. Advanced Email and Phishing Protection
Email remains a top attack vector, making advanced protection critical for business network security. Deploy anti-phishing measures such as SPF, DKIM, and DMARC for email authentication.
- Use AI-powered platforms to detect sophisticated threats.
- Train employees with simulated phishing campaigns.
- Integrate incident response workflows for reported threats.
Continuous phishing training reduces susceptibility, as shown in recent research, reinforcing your human firewall. Business Email Compromise causes massive losses, highlighting the need for layered defenses and ongoing awareness.
7. Data Backup, Recovery, and Business Continuity
Resilient data backup and recovery plans are essential for business network security. Automated, encrypted backups—both cloud and local—protect against data loss from ransomware and other disasters.
- Test disaster recovery plans regularly.
- Use immutable backups for ransomware resilience.
- Ensure compliance with data retention regulations.
Frequent testing and rapid restore capabilities ensure minimal downtime. Adhering to backup best practices supports business continuity and regulatory obligations.
Emerging Technologies and Trends Shaping Network Security
Emerging technologies are rapidly transforming the landscape of business network security. Staying ahead of these trends is critical for organizations seeking to defend against evolving threats. In this section, we examine how artificial intelligence, Zero Trust, SASE, and IoT security are shaping the future of business network security.

Artificial Intelligence and Machine Learning in Security
Artificial intelligence and machine learning are revolutionizing business network security by enabling faster, smarter threat detection. AI-driven platforms analyze massive volumes of network data, spotting anomalies and suspicious behaviors that might otherwise go unnoticed.
For example, AI can drastically reduce the time it takes to identify and contain threats, minimizing potential damage. These systems also help lower false positives, allowing security teams to focus on genuine risks. However, the rapid rise of AI also introduces new challenges, particularly in cloud environments. As highlighted in recent research, AI fueling surge in cloud security risks, organizations must adapt their business network security strategies to address vulnerabilities created by generative AI tools.
Despite AI's strengths, human oversight remains essential to interpret results and respond effectively to incidents.
Zero Trust Network Access (ZTNA) and Software-Defined Perimeter
Zero Trust Network Access is reshaping business network security by eliminating the assumption of trust within the network. Instead, every user and device must be continuously verified before gaining access to resources.
ZTNA and software-defined perimeter solutions provide granular access controls, ensuring users only reach the information they need. This approach limits the potential impact of breaches by preventing lateral movement across the network. For example, making infrastructure invisible to unauthorized users significantly reduces the overall attack surface.
Organizations adopting Zero Trust models are better equipped to safeguard sensitive data, especially as remote work and BYOD trends expand the boundaries of business network security.
Cloud Security and Secure Access Service Edge (SASE)
The shift to cloud-based operations is driving the adoption of Secure Access Service Edge architectures. SASE integrates network and security functions into a unified cloud-delivered platform, streamlining business network security for hybrid and multi-cloud environments.
A typical SASE solution combines SD-WAN, firewalls, CASB, and ZTNA, providing comprehensive protection for cloud workloads and SaaS applications. This approach not only improves visibility but also reduces the risk of misconfigurations, a leading cause of cloud breaches.
By consolidating security controls, organizations can better enforce policies and adapt to evolving business network security requirements as digital transformation accelerates.
IoT and OT Security Challenges
The proliferation of Internet of Things and operational technology devices presents new business network security challenges. Each connected device, from smart sensors to industrial controllers, represents a potential entry point for attackers.
To mitigate these risks, organizations must implement robust device authentication, network segmentation, and continuous monitoring. Isolating IoT devices from critical infrastructure helps prevent breaches from spreading. Regulatory bodies are also introducing stricter guidelines for IoT security to protect sensitive data and ensure business continuity.
Addressing these challenges requires ongoing investment in tools and policies that can adapt as the IoT landscape evolves, keeping business network security resilient and future-ready.
Compliance, Regulations, and Security Frameworks for 2026
Keeping up with compliance and regulatory demands has never been more crucial for business network security. Companies face a growing web of requirements, and understanding these standards is essential for safeguarding operations, maintaining trust, and avoiding costly penalties.
Navigating Global and Industry-Specific Regulations
The regulatory landscape for business network security is evolving rapidly. Organizations must comply with laws like GDPR for data privacy, NIS2 for critical infrastructure, HIPAA for healthcare, SOC2 for service providers, and ISO 27001 for information security management.
| Regulation | Focus Area | Key Requirement |
|---|---|---|
| GDPR | Data Privacy | User consent, data protection |
| NIS2 | Critical Infrastructure | Risk management, incident reporting |
| HIPAA | Healthcare Data | Patient confidentiality |
| SOC2 | Service Providers | Security, availability |
| ISO 27001 | Information Security | ISMS framework |
New mandates, such as NIS2, require stricter controls and faster incident reporting. Fines for non-compliance can be severe, making proactive business network security a top priority for all industries.
Building a Culture of Security and Awareness
A strong culture of security is foundational for effective business network security. Ongoing awareness training empowers employees to recognize threats and respond appropriately. Use platforms like KnowBe4 to simulate phishing attacks and reinforce learning through real-world examples.
Best practices include:
- Scheduling regular security workshops
- Encouraging prompt reporting of suspicious activity
- Recognizing and rewarding secure behaviors
Leadership involvement is key. When executives prioritize business network security, it sets the tone for accountability and vigilance across the organization.
Incident Response Planning and Testing
No business network security strategy is complete without a robust incident response plan. Develop and document clear protocols for identifying, containing, and recovering from security events. Conduct regular tabletop exercises and simulate breaches to ensure teams are prepared.
A simple incident response checklist includes:
1. Detect incident
2. Notify stakeholders
3. Contain threat
4. Eradicate risk
5. Recover operations
6. Review and improve
Businesses that test their plans recover faster and suffer less disruption, making incident readiness a vital part of ongoing security efforts.
Security Frameworks and Best Practices
Adopting recognized frameworks is a cornerstone of business network security. The NIST Cybersecurity Framework, CIS Controls, and ISO 27001 provide structured guidance for protecting assets and responding to threats. Tailor these frameworks to your organization's size, industry, and risk profile.
For efficient risk prioritization, consider integrating tools like the Vulnerability Management Chaining framework, which offers actionable insights into proactive vulnerability management.
Continuous improvement, regular audits, and adapting controls as business needs evolve ensure your business network security remains resilient in the face of emerging challenges.
Step-by-Step Implementation: Building a Secure Business Network
Building robust business network security is a journey, not a one-time project. By following a structured, step-by-step approach, organizations can systematically strengthen their defenses, protect sensitive data, and ensure compliance. Here is a practical roadmap to guide your implementation and future-proof your business network security.
Step 1: Assess Current Network Security Posture
The first step in business network security is understanding your current environment. Conduct comprehensive risk assessments and vulnerability scans across all network segments and devices. Inventory every asset, including servers, endpoints, cloud services, and user accounts.
Use automated tools to baseline your network and identify gaps in existing controls or policies. Analyze data flows to pinpoint where sensitive information resides and how it moves. Prioritize risks based on potential business impact, focusing on areas most likely to be targeted.
Regular assessments lay the groundwork for effective business network security, ensuring you address actual vulnerabilities rather than perceived threats.
Step 2: Develop a Customized Security Roadmap
With a clear understanding of your security posture, develop a tailored roadmap for business network security improvements. Align your initiatives with business objectives, compliance requirements, and risk tolerance.
Set measurable goals, milestones, and key performance indicators. Map specific security controls to relevant regulations such as GDPR or HIPAA. Engage stakeholders from IT, compliance, and executive leadership to ensure buy-in and accountability.
A well-crafted roadmap provides direction and clarity, helping your organization make informed decisions and track progress in business network security.
Step 3: Deploy Core Security Technologies
Implementing the right technologies forms the backbone of business network security. Start with centralized identity and access management, multi-factor authentication, and advanced endpoint protection.
Integrate network segmentation to limit lateral movement. Deploy secure remote access solutions and real-time monitoring tools. Use centralized dashboards for unified visibility and control, ensuring scalability as your business grows.
Choosing and deploying the right mix of technologies is crucial for maintaining resilient business network security in an evolving threat landscape.
Step 4: Establish Policies, Procedures, and Training
Effective business network security depends on clear policies and informed users. Develop enforceable security policies covering acceptable use, BYOD, remote access, and data handling.
Schedule regular employee training sessions, including simulated phishing exercises to build awareness. Document incident response protocols and ensure all staff know how to report suspicious activities.
Continuous education and clear procedures empower your team to act as a frontline defense, greatly reducing the risk of human error in business network security.
Step 5: Monitor, Test, and Continuously Improve
Ongoing vigilance is essential for business network security. Set up real-time monitoring and automated alerting to detect suspicious activity quickly. Conduct regular penetration tests and red team exercises to uncover hidden weaknesses.
Implement robust log management and SIEM systems for comprehensive threat detection. Review your security posture quarterly, updating controls and policies as threats evolve.
Continuous improvement ensures that business network security adapts to new challenges, minimizing risks over time.
Step 6: Backup, Recovery, and Business Continuity Planning
A resilient business network security strategy includes reliable backups and recovery plans. Automate backups to both cloud and offsite locations, ensuring data is encrypted and regularly tested for restorability.
Maintain immutable backups to prevent ransomware tampering. Align recovery objectives with business priorities for minimal disruption during incidents.
Proactive backup and continuity planning safeguard your organization from data loss, supporting uninterrupted business network security operations.
Step 7: Partner with Managed IT Security Providers
For many organizations, partnering with experts is the key to scalable business network security. Evaluate managed security service providers (MSSPs) for their expertise, 24/7 monitoring capabilities, and advanced threat intelligence.
Leverage external support for compliance management and incident response. Consider local providers for personalized service and rapid onsite support.
By collaborating with trusted partners, you can extend your business network security capabilities and free internal resources for core business functions.
Partnering with Delphi Systems Inc. for Managed Network Security
Delphi Systems Inc. specializes in managed IT services for small businesses in Lethbridge and surrounding areas, delivering proactive network monitoring, cyber defense, and data backup solutions.
Their fixed-rate fee structure enables predictable budgeting and comprehensive support. By outsourcing business network security to Delphi Systems, you gain access to expert teams, rapid incident response, and cutting-edge security technologies from leading vendors.
With local expertise and personalized service, Delphi Systems helps reduce downtime, ensure compliance, and keep your business network security strong in an ever-changing threat environment.
Future-Proofing: Preparing for the Next Generation of Threats
Looking ahead, business network security must evolve to counter increasingly sophisticated threats. Organizations that proactively adapt will be better positioned to withstand emerging risks and protect their digital assets. This section explores how to anticipate new attack vectors, leverage automation, foster learning, and plan strategically for long-term resilience.
Anticipating Future Attack Vectors
In the coming years, attackers will increasingly use AI-driven techniques, deepfakes, and supply chain compromises to target organizations. For business network security to remain effective, it must evolve to detect and counter these novel threats.
Adaptive security models that incorporate proactive threat intelligence are essential. For example, attackers often exploit third-party vendors and APIs, making it vital to assess external risks as part of your defense strategy.
Investing in research and emerging defense technologies can help businesses stay a step ahead. Regularly reviewing threat reports and collaborating with industry peers builds a stronger, more informed security posture.
Security Automation and Orchestration
Automation is transforming business network security by streamlining routine tasks such as patch management, incident response, and compliance reporting. Deploying Security Orchestration, Automation, and Response (SOAR) platforms enables faster threat detection and response.
For instance, automated containment can reduce breach response time from hours to minutes. However, skilled staff remain crucial to oversee these systems and address complex incidents that require human judgment.
Combining automation with expert oversight ensures organizations can respond quickly while maintaining accuracy and effectiveness in their security operations.
Investing in Continuous Learning and Innovation
Continuous learning is a cornerstone of robust business network security. Staying informed about the latest trends, tools, and best practices ensures defenses keep pace with evolving threats.
Encouraging staff to pursue certifications and ongoing training builds a knowledgeable team. Studies show that businesses with dedicated security teams experience fewer incidents and recover more quickly from attacks.
Fostering a culture of innovation and agility empowers organizations to adapt their security strategies as the threat landscape shifts.
Strategic Planning for Long-Term Resilience
Long-term business network security requires aligning security planning with business growth and digital transformation. Regular reviews of security strategies, including annual assessments and board-level reporting, help organizations stay ahead of new risks.
Executive support and cross-functional collaboration are critical for success. By involving leadership and all relevant stakeholders, businesses can create adaptable plans that evolve with technology and regulatory changes.
Strategic planning ensures that security remains a foundational element of organizational resilience.
As you look to strengthen your business network security for 2026 and beyond, remember that the right strategies and expert support can make all the difference. We understand how daunting it can be to keep up with evolving threats, manage compliance, and ensure your technology stays resilient. That’s why partnering with a trusted local provider like Delphi Systems Inc. lets you focus on what you do best, while we handle the complex task of safeguarding your IT environment. If you have questions or want to talk through your next steps, let’s connect—Call us now.





